Python Ethical Hacking - VULNERABILITY SCANNER(2)
VULNERABILITY_SCANNER
How to discover a vulnerability in a web application?
1. Go into every possible page.
2. Look for ways to send data to web application(URL + Forms).
3. Send payloads to discover vulnerabilities.
4. Analyze the response to check of the website is vulnerable.
->General steps are the same regardless of the vulnerability.
Class Scanner.
#!/usr/bin/env python import requests
import re
from urllib.parse import urljoin class Scanner:
def __init__(self, url):
self.target_url = url
self.target_links = [] def extract_links_from(self, url):
response = requests.get(url)
return re.findall('(?:href=")(.*?")', response.content.decode()) def crawl(self, url):
href_links = self.extract_links_from(url)
for link in href_links:
link = urljoin(url, link) if "#" in link:
link = link.split("#")[0] if self.target_url in link and link not in self.target_links:
self.target_links.append(link)
print(link)
self.crawl(link)
Vulnerability scanner.
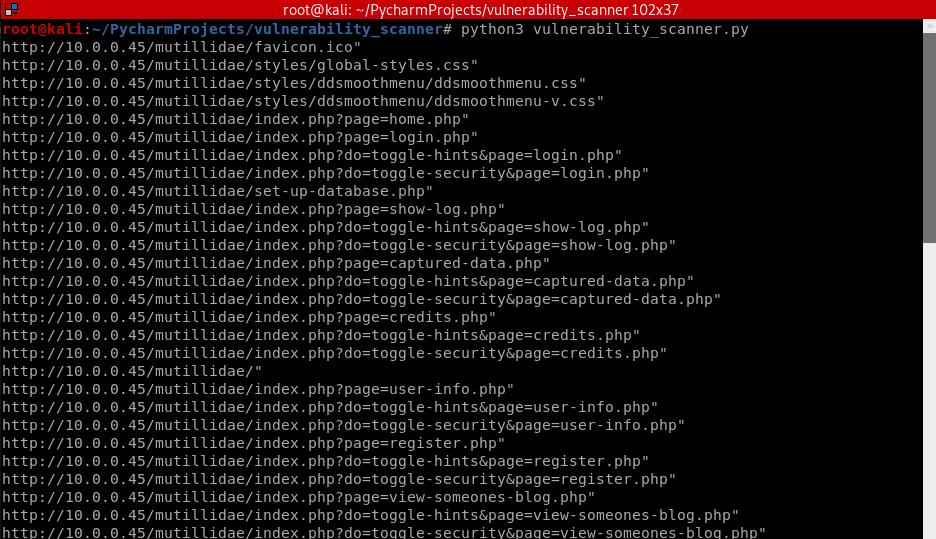
#!/usr/bin/env python import scanner target_url = "http://10.0.0.45/mutillidae/"
vuln_scanner = scanner.Scanner(target_url)
vuln_scanner.crawl(target_url)
The Python program runs fine.
Polish the Python code using Default Parameters.
Class Scanner.
#!/usr/bin/env python import requests
import re
from urllib.parse import urljoin class Scanner:
def __init__(self, url):
self.target_url = url
self.target_links = [] def extract_links_from(self, url):
response = requests.get(url)
return re.findall('(?:href=")(.*?")', response.content.decode()) def crawl(self, url=None):
if url == None:
url = self.target_url
href_links = self.extract_links_from(url)
for link in href_links:
link = urljoin(url, link) if "#" in link:
link = link.split("#")[0] if self.target_url in link and link not in self.target_links:
self.target_links.append(link)
print(link)
self.crawl(link)
Vuln_scanner:
#!/usr/bin/env python import scanner target_url = "http://10.0.0.45/mutillidae/"
vuln_scanner = scanner.Scanner(target_url)
vuln_scanner.crawl()
Python Ethical Hacking - VULNERABILITY SCANNER(2)的更多相关文章
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
- Python Ethical Hacking - VULNERABILITY SCANNER(7)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(4)
Extracting & Submitting Forms Automatically Target website:http://10.0.0.45/dvwa/vulnerabilities ...
- Python Ethical Hacking - VULNERABILITY SCANNER(8)
Implementing Code To Discover XSS in Parameters 1. Watch the URL of the XSS reflected page carefully ...
- Python Ethical Hacking - VULNERABILITY SCANNER(3)
Polish the Python code using sending requests in a session Class Scanner. #!/usr/bin/env python impo ...
- Python Ethical Hacking - VULNERABILITY SCANNER(1)
HTTP REQUESTS BASIC INFORMATION FLOW The user clicks on a link. HTML website generates a request(cli ...
- Python Ethical Hacking - VULNERABILITY SCANNER(6)
EXPLOITATION - XSS VULNS EXPLOITING XSS Run any javascript code. Beef framework can be used to hook ...
- Python Ethical Hacking - VULNERABILITY SCANNER(5)
EXPLOITATION - XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript cod ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- go 项目目录结构
网上有很多误人子弟的教程, 说项目下必须要有src, 傻逼玩意. 正确的路径应该是这样的: 所有go项目路径 src 项目1 项目2 项目N pkg bin 不是所有项目下必须建src, pk ...
- vs2017离线包下载获取方法
一.去官网下载所需要的版本的安装包获取程序: https://www.visualstudio.com/zh-hans/downloads/ 三个版本,对应文件名称为: 社区版:vs_Communit ...
- Sharding-JDBC 快速入门第一课
1. 概述 ShardingSphere是一套开源的分布式数据库中间件解决方案组成的生态圈,它由Sharding-JDBC.Sharding-Proxy和Sharding-Sidecar(计划中)这 ...
- 利用salt进行系统初始化操作
使用salt对系统进行初始化操作 概述 使用cobbler安装的操作系统,默认安装了一些基本的软件,比如zabbix-agent.salt-minion等,还没有对系统进行基本的初始化操作,为了实现标 ...
- disruptor架构四 多生产者多消费者执行
1.首先介绍下那个时候使用RingBuffer,那个时候使用disruptor ringBuffer比较适合场景比较简单的业务,disruptor比较适合场景较为复杂的业务,很多复杂的结果必须使用di ...
- HDU 5969 最大的位或【贪心】
题目 B君和G君聊天的时候想到了如下的问题. 给定自然数l和r ,选取2个整数x,y满足l <= x <= y <= r ,使得x|y最大. 其中|表示按位或,即C. C++. Ja ...
- ADAS感知开发问题
ADAS感知开发问题 1. 雨天相机 问题:雨天相机目标识别不稳.出现目标时断时续的情况 对策: 增加单雷达生成功能.当单雷达目标置信度高时直接由雷达生成目标. 2. 相机震动目标位置突变 问题 :相 ...
- Mac上使用Docker Desktop启动Kubernetes,踩坑后终于搞掂
1 前言 Kubernetes又简称k8s,是Google开源的容器集群管理系统,最近也是火热.闲来无事(为了发文),捣鼓了一下,在Mac上搭建Kubernetes,遇到一些坑,也记录一下. 另外,D ...
- .net core Web API参数绑定规则
参数推理绑定 先从一个问题说起,微信小程序按照WebAPI定义的参数传递,Get请求服务器端可以正常接收到参数,但是Post请求取不到. Web API代码(.netcore 3.1)如下: [Htt ...
- js element类型的属性和方法整理
Element类型 除了Document类型,我们Web编程中最常用的类型就是Element类型啦.Element 类型用于表现XML或HTML元素,提供了对元素标签名,子节点,特性的访问 特征 no ...
