Ethical Hacking - NETWORK PENETRATION TESTING(4)
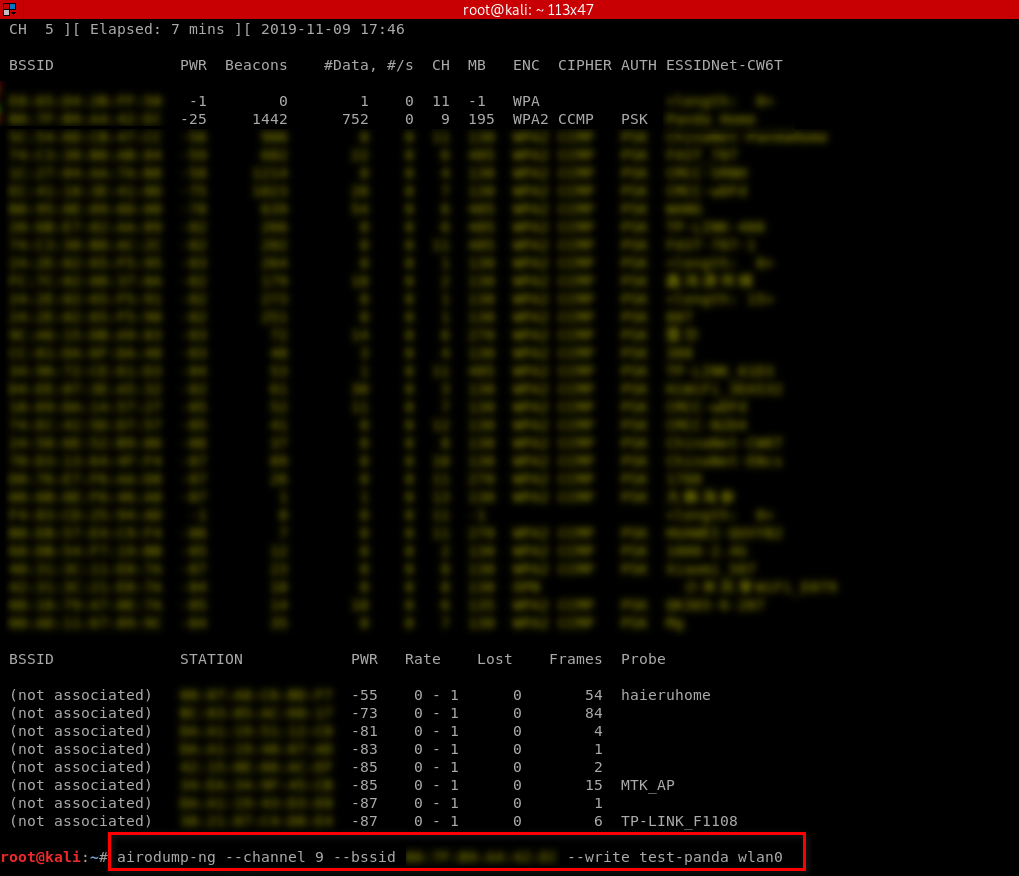
Targeted packet sniffing
airodump-ng --channel[channel] --bssid[bssid] --write[file-name][interface]
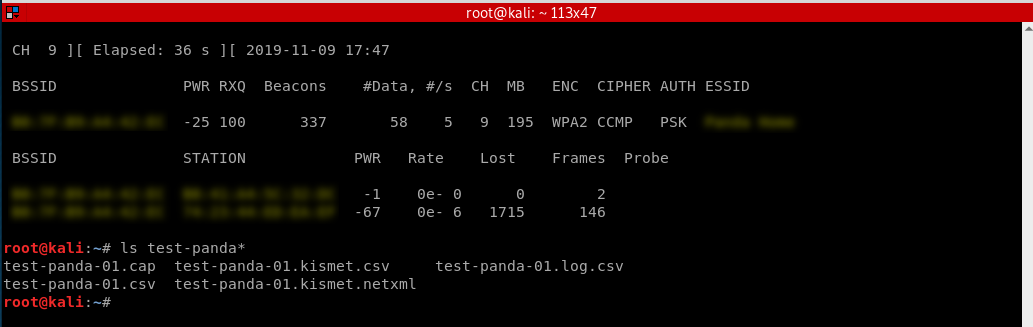
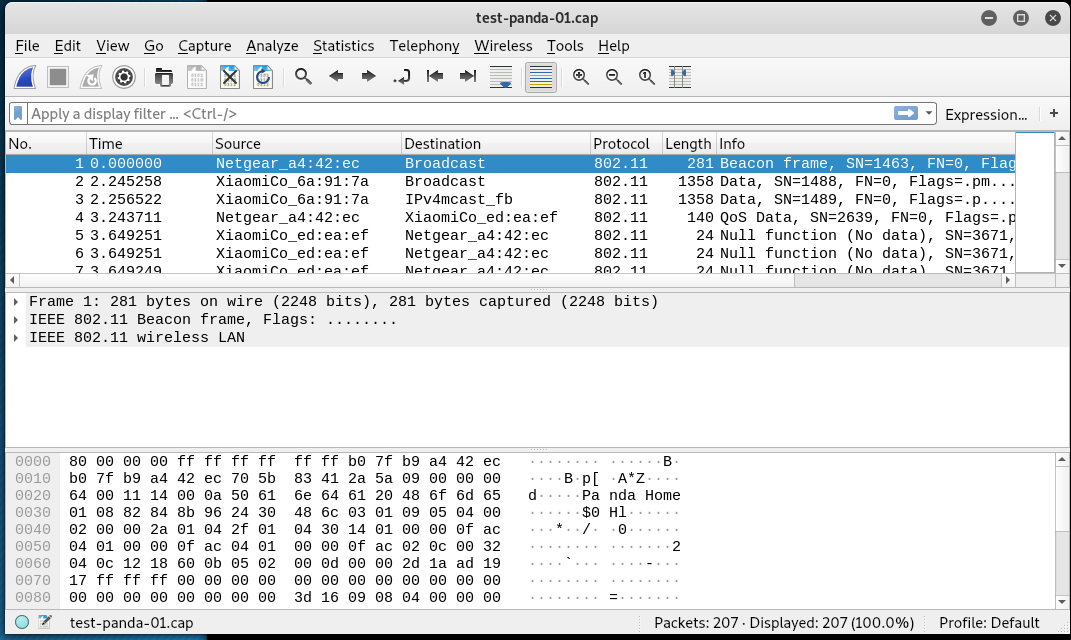
Now all the data will be stored in the file name specified after the -write option. We can analyze this data using Wireshark. The only problem is that the collected data will not be much of use if the target network uses encryption.
Monitor my home Wi-Fi as a sample.
Stop the monitor and find the packets.
Open the captured packets through WireShark and analyze.
Ethical Hacking - NETWORK PENETRATION TESTING(4)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- 11、vue-路由
1.路由: 官方提供一个插件,构建单页面应用,主要实现得功能页面得切换.组件得跳转 2.vue中得路由:vue-router包,如果是脚手架进行搭建得,那么是不需要安装vue-router这个包得,因 ...
- 如何解决jeecgBoot前端运行项目之后无法获取验证码的问题
我也是第一次接触这个开源项目,拿到项目之后,安装完环境和依赖,当我启动项目的时候,验证码却刷新不出来. 然后公司后端告诉我需要改两个接口,一个是public目录下的index.html和vue.con ...
- 深入理解JVM(③)虚拟机的类加载时机
前言 Java虚拟机把描述类的数据从Class文件加载到内存,并对数据进行校验.转换解析和初始化,最终形成可以被虚拟机直接使用的Java类型,这个过程被称为虚拟机的类加载机制. 类加载的时机 一个类型 ...
- mybatis缓存之一级缓存(一)
对于mybatis框架.仿佛工作中一直是在copy着使用.对于mybatis缓存.并没有一个准确的认知.趁着假期.学习下mybatis的缓存.这篇主要学习mybatis的一级缓存. 为什么使用缓存 其 ...
- SQL注入之报错注入常见函数
- SQL注入基础原理
Web安全: 三层架构(3-tier architecture) 通常意义上就是将整个业务应用划分为: 界面层(User Interface layer) 业务逻辑层(Business Logic L ...
- django 类视图的使用
使用django框架也有挺长时间了,但是一直都没有用过django的类视图,因为之前跟着网上教程学习时,觉得类视图是进阶的知识,可能目前还达不到吧 但今天在做项目的时候用到了,感觉真的太方便了吧,而且 ...
- html实现时间轴_纯css实现响应式竖着/垂直时间抽布局效果
1.概述 html实现用时间点来展示事件发生点来代替用table展示一条条数据,能够给人清晰.一目了然能够看清事情发生的过程,UI页面也显示的那么清晰.如何用css+html做出时间轴展示事件点的?先 ...
- 逻辑式编程语言极简实现(使用C#) - 4. 代码实现(完结)
本文是本系列的完结篇.本系列前面的文章: 逻辑式编程语言极简实现(使用C#) - 1. 逻辑式编程语言介绍 逻辑式编程语言极简实现(使用C#) - 2. 一道逻辑题:谁是凶手 逻辑式编程语言极简实现( ...
- 洛谷 P1131 [ZJOI2007]时态同步 树形DP
题目描述 分析 我们从根节点开始搜索,搜索到叶子节点,回溯的时候进行维护 先维护节点的所有子节点到该节点最大边权(边权为叶子节点到同时到达它所需要时间) 然后维护答案,答案为最大边权减去所有到子节点的 ...
